This is a focus on data security—how it's changed, what it means today, and how organizations are grappling with it. It's also a hard look at our perspectives— the difference between widely held beliefs and what is really happening on the front lines.
Select A region to EXPLORE
- Global
- AMER
- EMEA
- APAC
Rubrik Zero Labs strives to deliver actionable, vendor-agnostic insights to help reduce data security risks. We incorporated findings from different sources, all covering 01 January through 31 December 2022.
5000+
Customers
22
Industries
19+bn
Sensitive data records
We use Rubrik telemetry to stay close to the ground truth of everyday organizations while also providing context about our bias.
22
Industries
5000+
Customers
3
regions
57
countries
Total volume of data secured:
28
659
28 EB vs 659 BEPB
AKA Hey Nerds!!!
When most of the world hears "data," they imagine logical storage, also known as frontend storage. Those of us in the data business focus on backend storage.
Rubrik takes the entirety of an organization's data and performs different functions—including deduplication and compression—to reduce the amount of data placed in backend storage. That's why we'll focus on backend storage throughout the rest of this report.
A Sense of Scale:
Some estimates say every word ever spoken across all of history in every language equates to 5 EB…or just 18% of the data secured by Rubrik in 2022. 1234
Sensitive data located in:
8.7+
billion files
19+
billion sensitive data records within the files
1 of every 38 files contains sensitive data
Case Study:
We also took a closer look at an attack against one of the organizations included in the Rubrik telemetry. The organization's name has been changed to protect its privacy.
Rubrik telemetry data = RT
(1) https://www.space.com/18383-how-far-away-is-jupiter.html (2) https://www.sizes.com/tools/filing_cabinets.htm (3) https://www.zmescience.com/science/how-big-data-can-get/ (4) https://www.backblaze.com/blog/what-is-an-exabyte/
1600+
IT and Security Leaders
10
Countries
49%
CIOs and CISOs
We commissioned a survey conducted by Wakefield Research to round out our Rubrik telemetry with a broader view of the data security landscape. We chose to engage IT and security leaders to study the difference in their perspectives.
1600+
leaders
49% CIOs and CISOs

16% VPs

38% Senior Directors or Directors

Conducted across three regions:
AMER
EMEA
APAC
and 10 countries:
United States
United Kingdom
France
Germany
Italy
Netherlands
Japan
Australia
Singapore
India
Wakefield research data = WR
We engaged respected cybersecurity organizations for a more holistic view of the data security landscape. We appreciate the use of their findings.
Palo Alto Networks Unit 42
Mandiant
Expel
Permiso
We engaged respected cybersecurity organizations for a more holistic view of the data security landscape. We appreciate the use of their findings.
Palo Alto Networks Unit 42
2022 Ransom demands from 2023 Unit 42 Ransomware and Extortion Report
Mandiant
Global median dwell times and ransomware investigation ratios from M-Trends 2023
Expel
Ransomware precursor activity and growth of intrusions in public clouds from Great Expeltations 2022
Permiso
Illicit credential use in cloud intrusions and credential privilege levels from Permiso 2022 - End of Year Observations
Event response data = ER
The Data Seascape
Organizations are sitting on an ocean of data. On the surface that ocean looks vast, yet stable.
But anyone dropped into its depths knows that it's teeming with life.
Vision is limited, but the more you look, the more data you'll find—in caves, under rocks, nearly everywhere. The currents are swift. It's never the same scene twice.
Data is growing faster and in more places than we think RT
45%
secure data in a mix of on-premises, cloud, and SaaS.
36%
use multiple cloud vendors concurrently.
For each data security solution, there's a follow-on challenge.WR
The last line of defense during a crisis is the data backup and recovery systems with it's associated processes. But organizations are finding that simply having a backup solution isn't enough.
Everyone is "doing" data security, but the reality in 2022 is uneven. WR
of organizations employed at least one zero trust initiative.
tested backup and recovery options.
developed or reviewed an incident response plan.
created or refined data recovery orchestration.
These impacts and uncertainties are nagging at the back of our minds until one day ...
these fears actually appear
out of the depths to the surface.
A US-based educational organization experienced the harsh realities of data security first hand. Through their story, we'll explore just how common their experience is.

The facts in this case study are true, but the actual name of the organization has been anonymized to protect client privacy.
2.9
PB logical storage
64
BETB physically stored

Data in two distinct environments
155% data growth across 2022
Day 1-3
The Intrusion
Log4j
In late 2021, a vulnerability in one of the most deployed pieces of open-source software, Apache's Log4j software library, sent the technology industry into overdrive. Cybercriminals started exploiting this vulnerability, now labeled Log4Shell, within 12 hours and continue to exploit it to this day. 1
1 The Guardian: Recently uncovered software flaw 'most critical vulnerability of the last decade'
By accessing this server, the attackers successfully evaded the boundary infrastructure security measures.
Attackers used a mix of legitimate tools and processes to create illicit credentials, expand their access, create additional footholds across the environment, and compromise Active Directory.
The cybercriminals then moved laterally across Stone University gaining access to five distinct machines in their VMware environment and picking up key details along the way—
all without Stone University knowing.
Stone University's experience, while alarming, is surprisingly common compared to what many organizations faced last year.WR
99%
of IT and security leaders were made aware of at least one attack in 2022. On average,
leaders dealt with attacks 52 times in 2022.
61%
of these attacks affected SaaS applications, the most targeted platform / environment.
All environment types were affected by malicious activity with ratios of: RT
61%
SaaS
60%
Cloud
52%
On-Premises
According to Expel, malicious incidents in the three major public clouds increased by: ER
70%
Note: The three public cloud referenced are Amazon Web Services (AWS), Google Cloud Platform (GCP), and Microsoft Azure (Azure). 1
Once the cybercriminals gained access to Stone University's environment via the vulnerability, they quickly pivoted to malicious credential use. ER
Permiso reported that
100%
of the cloud intrusions they detected and responded to were the result of a compromised credential. 2
Additionally, these credentials were more than
90%
overprivileged, or, put another way, the credentials only used 5-10% of the amount of assigned privileges. 3
Most companies have little to no visibility into how their identities are used… they aren't monitored or audited…and aren't easily identified when compromised. With the growth of API-driven ecosystems such as CI/CD pipelines, microservices, and serverless architectures, these are being leaked and sprayed at a staggering rate, drastically increasing the number of compromised keys, tokens, and certificates.
Ian Ahl, VP and Head of P0 Labs, Permiso
(1) https://expel.com/blog/2023-great-expeltations-report-top-six-findings/ (2) https://permiso.io/blog/s/permiso-2022-end-of-year-observations/ (3) https://permiso.io/blog/s/permiso-2022-end-of-year-observations/
Day 4
Ransomware Preparation
Organizations often don't know they're under attack until the attackers tell them
Still undetected, Stone University's attackers prepared to make their presence known. They ensured they had multiple access points to Stone University's systems, so...

They also established access on a legacy data backup server to observe Stone University's response.
In a twist of fate, Stone University had previously replaced the backup vendor and technology, but left this server in place despite no longer needing it.
Finally, the cybercriminals exfiltrated eight gigabytes (GB) of data from across Stone University.
How common are ransomware events?
40% WR
40% of external organizations surveyed reported a successful ransomware event.
11% ER
Expel reported 11% of all malicious events encountered by their SOC were tied to ransomware activity. 1
18% ER
Mandiant reported 18% of their engagements were ransomware events. 2
Types of attacks external organizations faced in 2022: WR
59%
data breach
54%
business email compromise or fraudulent transfer
41%
insider event
40%
ransomware
Stone University attackers' actions are consistent with Mandiant's attacker median global dwell times: ER
Ransomware investigation dwell times are typically shorter because the attacker “self-reports” by sending the ransom note or encrypting an environment. 1
(1) https://www.mandiant.com/m-trends
Day 5
The Ransomware Deployment
Stone University's attackers began the ransom phases of their intrusion at approximately 9 pm on Sunday evening.
AvosLocker
AvosLocker is used to describe both a malware family and a threat group. It operates under a “Ransomware as a Service” model, where affiliates subscribe to a service to execute ransomware deployments and collect ransoms. In the case of AvosLocker, the subscription covers direct handling of ransom negotiations, publishing exfiltrated victim data, and the actual use of a specific ransomware tool. 1
1 CISA. "FBI and FinCEN Release Advisory on AvosLocker Ransomware | CISA." US-CERT, CISA, 22 March 2022. Accessed 8 November 2022.
AvosLocker also shut down the virtual machine management tools shortly before encrypting files to prevent Stone University from responding in an effective manner.
the attackers posted ransom notes demanding
Many people believe the encryption event is the end of the ransomware story, but that's almost never the case. For instance, cybercriminals possessed unfettered access in Stone University's systems for days, undetected. And it will take several more days until Stone University's ransomware story is fully resolved.
Ransomware is a type of data denial threat. Data denial can involve ransomware, wipers, data deletion using valid access, and denial of service efforts. Additionally, cybercriminals routinely exfiltrate data for a range of goals before encryption events.
In 2022, Rubrik's Ransomware Response Team assisted dozens of organizations with recovery operations. The most prevalent ransomware families in these responses were:
- LOCKBIT2.0
- BLACKCAT/ALPHV
- AVOSLOCKER
- META
- PLAY
- HIVE
- SPARTA
- BLACK BASTA
- SPIDER
- VICE SOCIETY
Day 5-7
Initial Response
Beating the attackers depends on your readiness to respond
To overcome this, they restored data to forensic and test environments to investigate and prioritize their next actions.
Stone University also analyzed their offline data backups, uncovered a suspected compromised server, and livemounted this server into the forensic environment for detailed analysis.
They found the attackers notes, complete with their compromise plan, compromised accounts, and timeframe. Additional forensics revealed seven more compromised servers and the initial compromise point.
Hopeful, Stone University began rapidly rebuilding their environment in two waves:
First, the actual compromised servers from the initial intrusion.
The Stone University team restored the eight compromised servers resident in five VMs from a point-in-time one day before attackers arrived, losing six total days of data.
Secondly, the servers that were encrypted with ransomware, but not part of the initial compromise.
This left the remaining 145 VMs-these required a less intensive response based on only suffering the encryption action. They were restored from backups taken just one day before the ransomware deployment, avoiding five additional days of lost data across these 145 VMs.
The overall recovery operation also required new ESXi hosts, a new vCenter, and an active directory rebuild.
Of all the possible outcomes, this was the best that Stone University could hope for. Optimistic about their progress, Stone University was determined not to pay the ransom
It can be easy to look past the first major hurdle in an encryption event:
How do you diagnose and analyze something that's encrypted? Does paying the ransom work? Being prepared for this initial encryption moment with clean copies of data provides opportunities. Stone University was prepared, but what factors into being ready for this moment?
Does Paying a Ransom Work? WR
46%
External organizations that paid a ransom saw limited returns using attacker-provided decryption solutions with 46% recovering half or less of their data via the attackers.
16%
Only 16% of all external organizations recovered all of their data via attacker decryption tools.
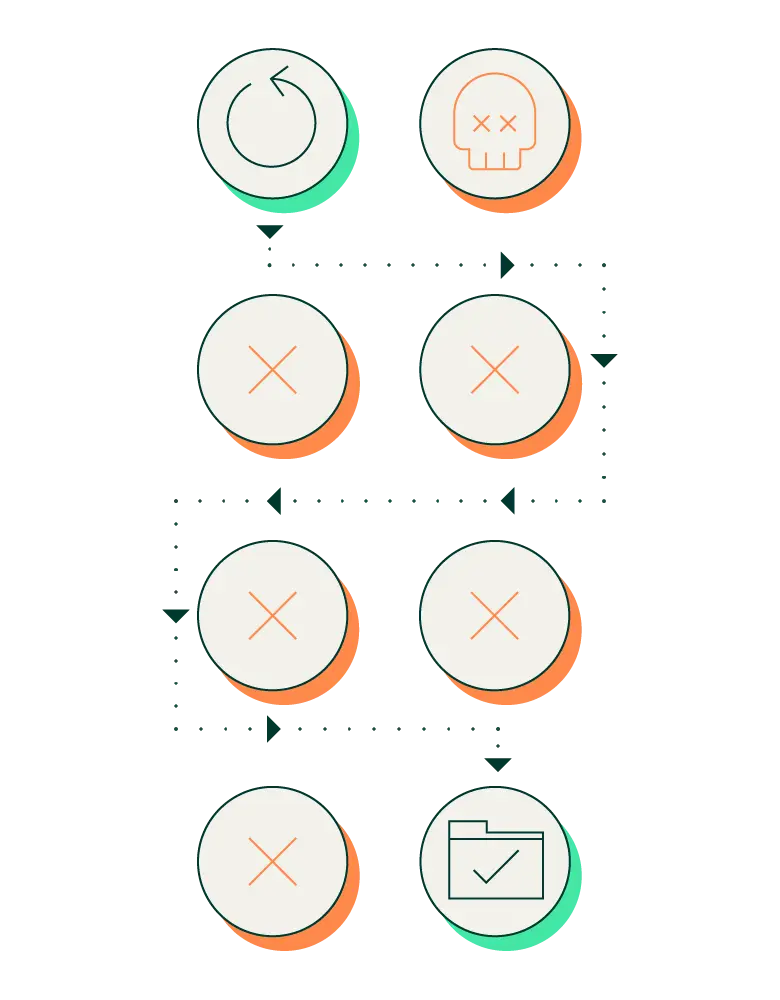
Rubrik telemetry revealed the prevalence of ransomware precursors and encryption rates: RT
Less than .004% of secured data encountered an encryption event
Anomalous behavior detection
Anomalous behavior detection is the first phase in a two-phase process for identifying ransomware. During this process, Rubrik analyzes file system metadata for anomalous behavior, such as an unusual number of files being added, deleted, or replicated. Most anomalous activity isn't ransomware, but needs follow-on investigation.
Suspicious file detection
The second phase of the two-phase ransomware identification process is suspicious file detection. This phase uses a combination of AI and machine learning to evaluate the files identified in the anomalous behavior detection phase for data entropy, file extensions, compression, known malicious ransomware actions, and a variety of other factors indicative of ransomware.
Snapshot analysis
A snapshot is a copy of the offline data backup and typically occurs on an automated, recurring pattern or in ad-hoc tasking. Analytics can then be performed against the completed snapshots.
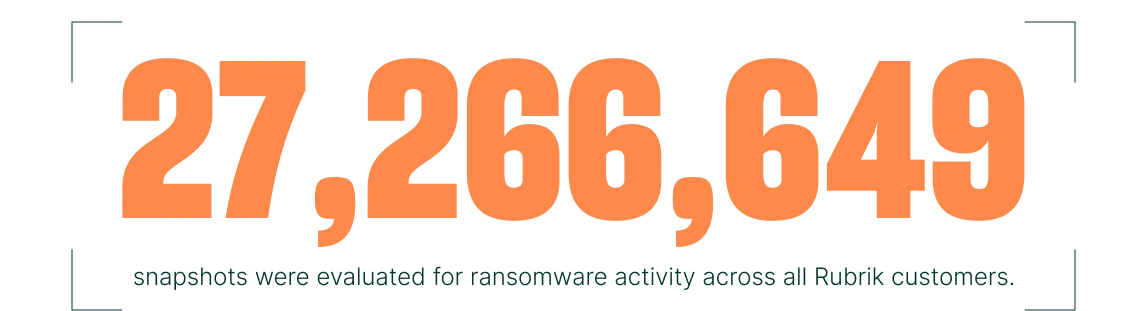
20,692
snapshots, or .07% of the total number of snapshots, contained anomalous activity.
1,198
of the anomalous snapshots, or 6% of all anomalous activity, led to a follow-on encryption event preventing the snapshot completion.
Of all the snapshots evaluated, only .004% had an encryption issue.
ALL
100% of the encryption events were tied to a lack of multi-factor authentication.
100%
All encryption events were previously identified as anomalous activity.
Across all Rubrik customers in 2022 RT
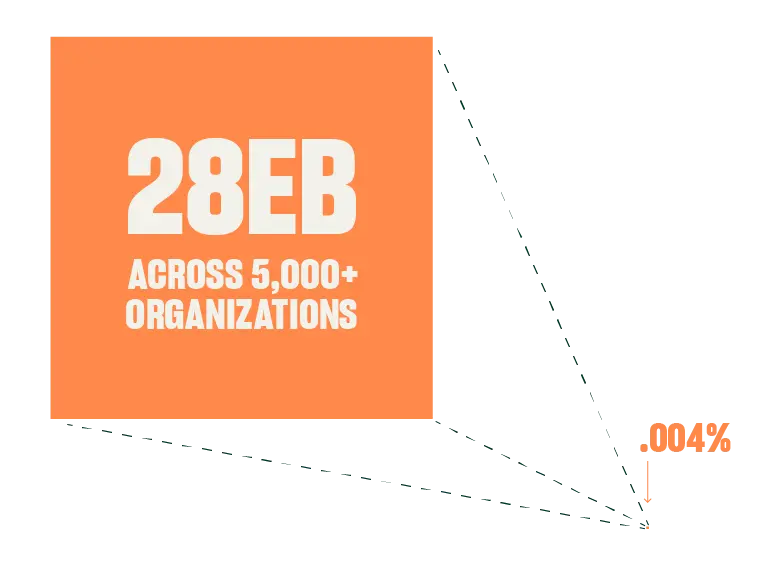
less than .004% of all data secured required further analysis or was indicative of ransomware activity.
This provides a snapshot (pun intended) of how an organization can gain control of its threat surface.
It's virtually impossible to remove your organization from the vast threat landscape, but it is more than possible to remove large swaths of your risk area from this attack surface.
Day 8
Second Ransom Demand
Encryption isn't the attacker's only (or preferred) weapon
DAYS AFTER
The original ransom demand, the attackers sent a second one. This ransom threatened to leak the 8GB of exfiltrated data to an AvosLocker controlled leak site if the ransom wasn't paid within four days.
The attackers also tried to compromise new portions of the Stone University environment in attempts to survive response actions.
After a hopeful start, this unexpected twist drove Stone University back to the beginning and left them with another tough decision:
Pay the ransom or see their data leaked online
72%
of non-Rubrik organizations reported paying a ransomware demand.
For non-Rubrik organizations who paid a ransom, the specific ransom ratios are: WR
40%
paid ransomware demand due to encryption events.
37%
paid ransomware demand due to extortion threats over data leaks.
2022 ransoms observed by Palo Alto Networks Unit 42 Incident Responses: ER

Highest ransomware demand

Highest ransoms paid 1
Day 8-11
Adjusted Response
Data visibility creates decision making opportunity
Stone University shifted their response to three distinct efforts to tackle the data extortion ransom demand.
 First, they conducted detection and response efforts to identify and counteract the follow-on intrusion efforts. This required replacing several servers, replacing multiple firewalls, and other hardening actions.
First, they conducted detection and response efforts to identify and counteract the follow-on intrusion efforts. This required replacing several servers, replacing multiple firewalls, and other hardening actions.
 Second, they continued data restoration efforts by testing portions of recovered environments then moving these portions into the production environment.
Second, they continued data restoration efforts by testing portions of recovered environments then moving these portions into the production environment.
 Third, Stone University started assessing the impact if the attacker posted the stolen data online.
Third, Stone University started assessing the impact if the attacker posted the stolen data online.
But...
Stone University couldn't determine the data leak threat in their production environment due to ongoing encryption issues, to include verifying if the attacker actually stole 8GB of data or what data was stolen.
So...
Instead, they shifted data impact discovery operations to their most recent data backup.
The good news
Stone University found answers within 24 hours and now had three days to make informed decisions.
The bad news
The attackers successfully stole 8 GB of data containing over 9 million sensitive data records ranging from 2013 to the present.
Having their sensitive data leaked would be a huge blow for Stone University, but they understood a hard-earned truth: there is no guarantee sensitive data wouldn't get posted even if they paid the ransom.
Instead, Stone University used the three days to proactively notify impacted individuals and organizations.
By the time the data leaked, Stone University had done the hard, but necessary work to conclude all major response actions...
Rapidly shifting and scattered data presents real risk for organizations. RT
A typical organization has
files containing sensitive data
and
sensitive data records total
Files vs. sensitive data records: Files contain data records. Some of those records can be sensitive. For example, one spreadsheet file can contain hundreds of sensitive data records, while other files might not contain any sensitive data.
Not only is every global organization sitting on a massive amount of data, some of that data would cause tremendous harm if suddenly unavailable or compromised.
One example is sensitive data: This is data derived from various industry standards or regulations—such as PII, HIPAA, GDPR, and CPAA. 1234
There are numerous challenges evaluating data impacts to consumers and organizations alike, but financial penalties for sensitive data offer one option. 567 Here are a few examples:
Penalty for sensitive data exposure: Up to 20 million Euros or 4% of global company revenue for severe violations, whichever is higher.
In a typical environment, it would take a fine of less than two Euros per record to reach 20 million Euros.
Penalty for sensitive data exposure: $50 to $50,000 USD per violation, with a max penalty of $1.5 million USD.
Using only the typical file average count, the $1.5 million USD maximum penalty is easily surpassed with a total of $28 million USD at the lowest $50 USD penalty.
Penalty for sensitive data exposure: Up to $2,500 USD per violation, or up to $7,500 for each intentional violation. No penalty cap.
A typical organization's file count alone would result in 1.1 billion USD in fines.
(1) https://gdpr-info.eu/art-4-gdpr/

Rubrik provides measurements of a cumulative data security score to its customers and sees an ongoing, positive trend in organizational improvement. The Data Security Score is calculated every 24 hours based on the following categories:
1
Platform Security: Measures the effectiveness of infrastructure security where data is stored and includes topics like user controls, administrative authentication, audit logs, etc.
2
Data Protection and Recovery: Analyzes how well the backup data is secured, if a clean copy of the latest backup is available, and other related factors.
3
Ransomware Investigation: Determines quality and frequency of ransomware threat monitoring and if this data can be recovered after an encryption event.
4
Sensitive Data Discovery: Measures how much sensitive data is being protected, access controls for this data, and if sensitive data is prioritized for recovery.
5
Scores are assessed as following:
- 0-50: Unsatisfactory
- 51-75: Needs Improvement
- 76-90: Satisfactory
- 91+: Excellent
A typical global organization saw their score increase from 51.2 to 59.47 in 2022, a 16% increase. RT
59.47 Overall Score Averages
16.2% Rate of improvement in 2022: 16.2%