Rubrik for Microsoft 365
End to End Cyber Resilience for Microsoft 365
Restore your Minimum Viable Business in minutes, not weeks. One platform to secure data, identity, posture, and AI agents with business-aware recovery to close critical resilience gaps.
End to End Cyber Resilience for M365
Ensure uninterrupted continuity across Exchange, SharePoint, OneDrive, and Teams. By unifying data, identity, and posture management, you automate recovery and harden your environment against modern threats and rogue AI.
Autonomous Business Recovery
Autonomously classify and recover mission-critical groups in minutes to restore your Minimum Viable Business.
Identity Resilience
Automate Entra ID and AD recovery to prevent lockout and ensure users can authenticate to resume mission-critical work instantly.
Data Access Governance
Harden posture and reduce blast radius. Proactively identify sensitive data risks and automate remediation before exploitation by adversaries.
AI Resilience
Instantly rewind Copilot errors to a clean state. Monitor interactions and enforce agent governance to remediate rogue AI actions and ensure continuity.
Data Resilience powered by Autonomous Business Recovery
Autonomously classify critical users and data to restore your Minimum Viable Business instantly, bypassing API throttling while other data recovers in the background.
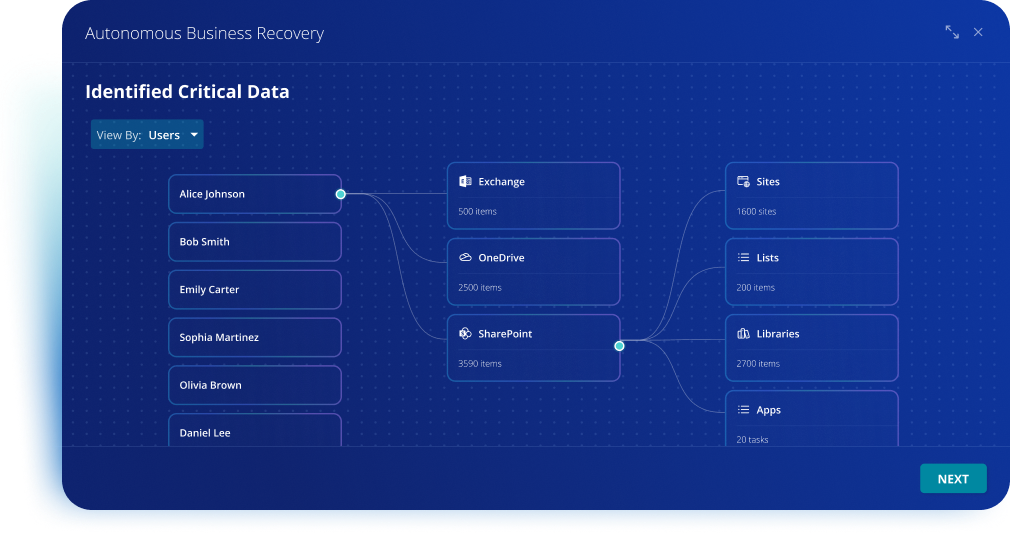
Restore Your Minimum Viable Business (MVB)
Autonomously classify and recover mission-critical groups like Executive Leadership, Legal, and Finance to restore core operations in minutes, not weeks.
Overcome SaaS API Bottlenecks
Bypass Microsoft 365 API limits and Graph API throttling through AI-driven automated orchestration, eliminating the technical bottlenecks that stall traditional tools.
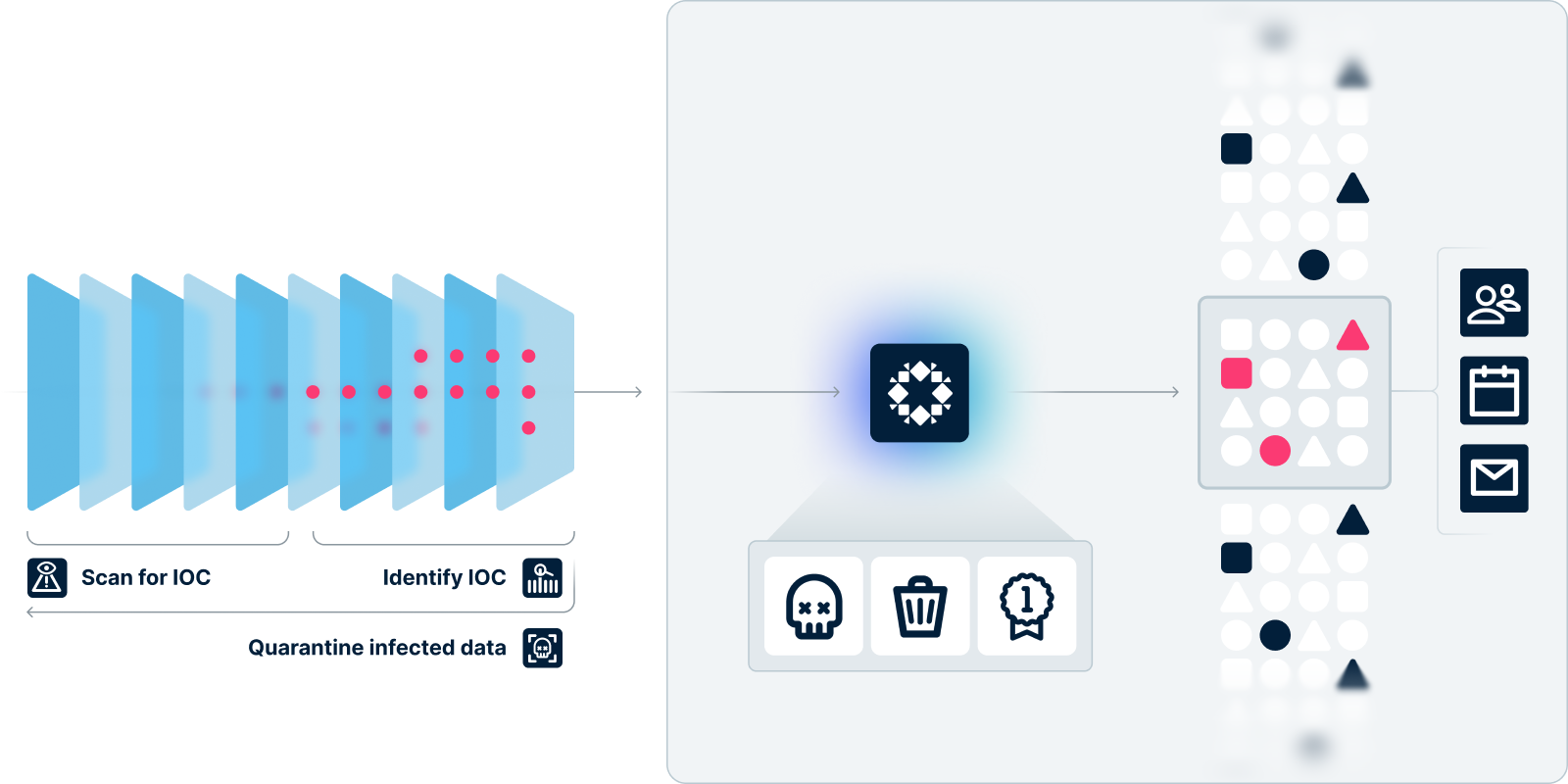
Continuous Threat Monitoring & Hunting
Identify threats and anomalies before escalation. Scan for Indicators of Compromise to isolate infected data and prevent reinfection during restoration.
M365 Data Recovery & Service Recoverability
Maintain M365 availability during tenant-level crises with recovery speeds up to 100x faster than native recovery, ensuring uninterrupted business continuity.
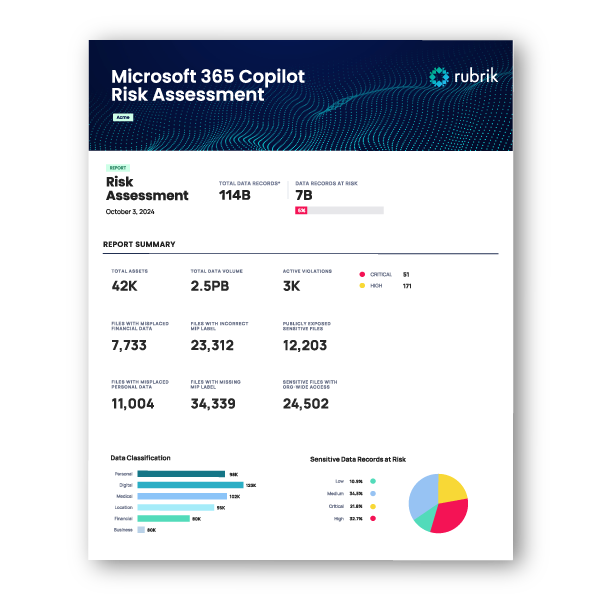
Microsoft 365 Copilot Free Risk Assessment
Ready to leverage AI tools like Copilot but concerned about data security? Get a free risk assessment to prepare your organization for secure Copilot adoption.
Orchestrate Identity Resilience
Ensure business continuity by securing the identities that power Microsoft 365. Automate Entra ID and AD recovery to prevent lockout and ensure users can authenticate to resume work instantly.
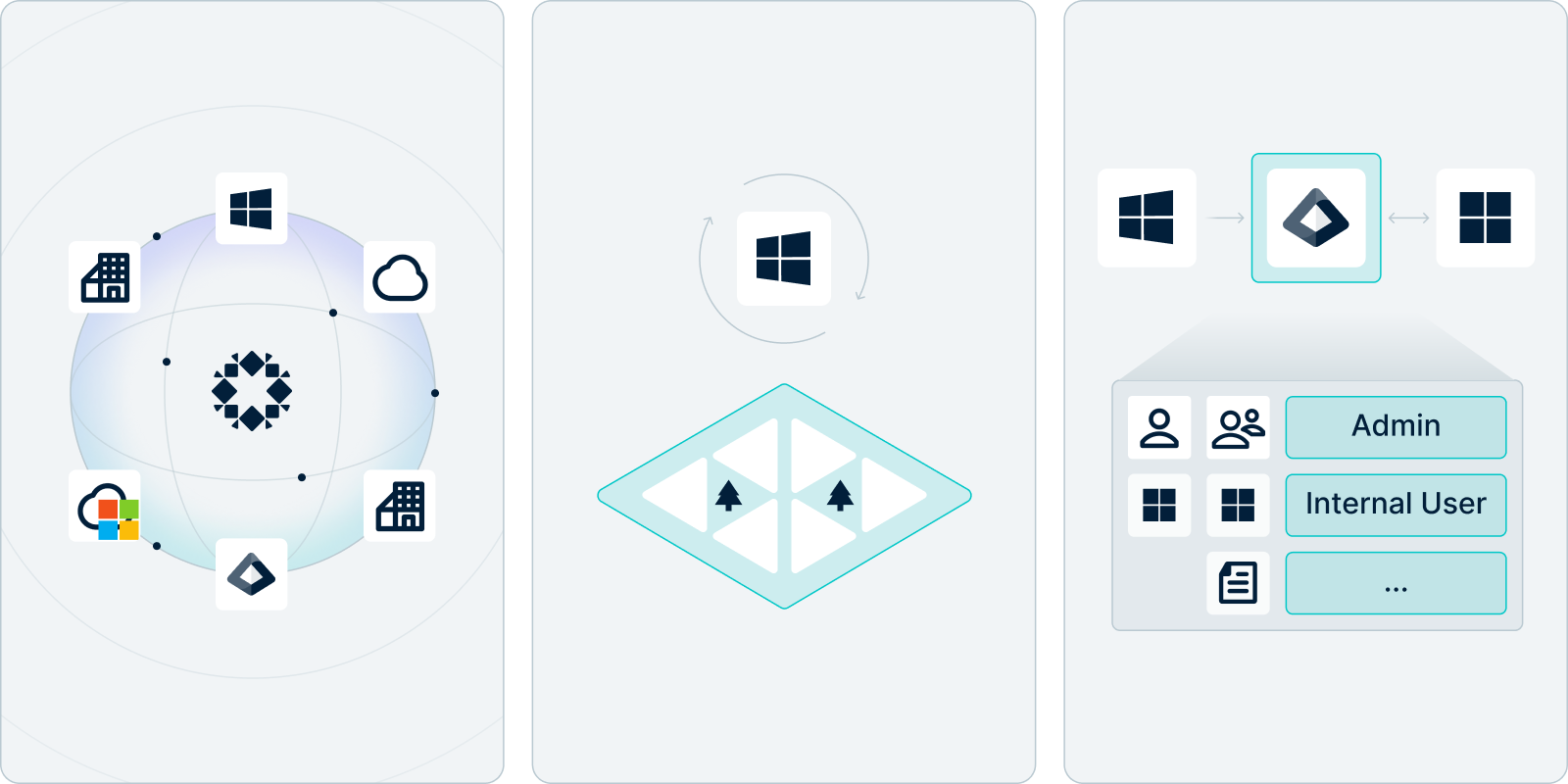
Granular Entra ID Recovery
Swiftly restore critical Entra ID objects; including users, groups, roles, and conditional access policies; to a clean state with precise, granular control.
Rapid Hybrid Forest Recovery
Orchestrate the recovery of Active Directory forests and domain controllers in five simple steps to ensure service availability across hybrid environments.
Restitch Identity Relationships
Automatically restitch relationship mapping and updates between on-prem AD and Entra ID to align service connections for seamless business resumption.
Data Access Governance
Reduce your blast radius by hardening security posture. Proactively identify and mitigate risks before exploitation by adversaries or rogue AI via automated remediation.
Sensitive Data Discovery at Scale
Automatically classify sensitive data based on business context. Integrate with Purview and MIP to categorize data as Confidential, General, or Public.
Strategic Policy Automation
Apply automated policies to minimize exposure. Identify overexposed personal files and receive real-time alerts on content missing critical labels.
Access Governance & Remediation
Visualize risky access with intuitive graphs. Instantly remove links to publicly shared data and trigger auto-labeling when violations are detected.
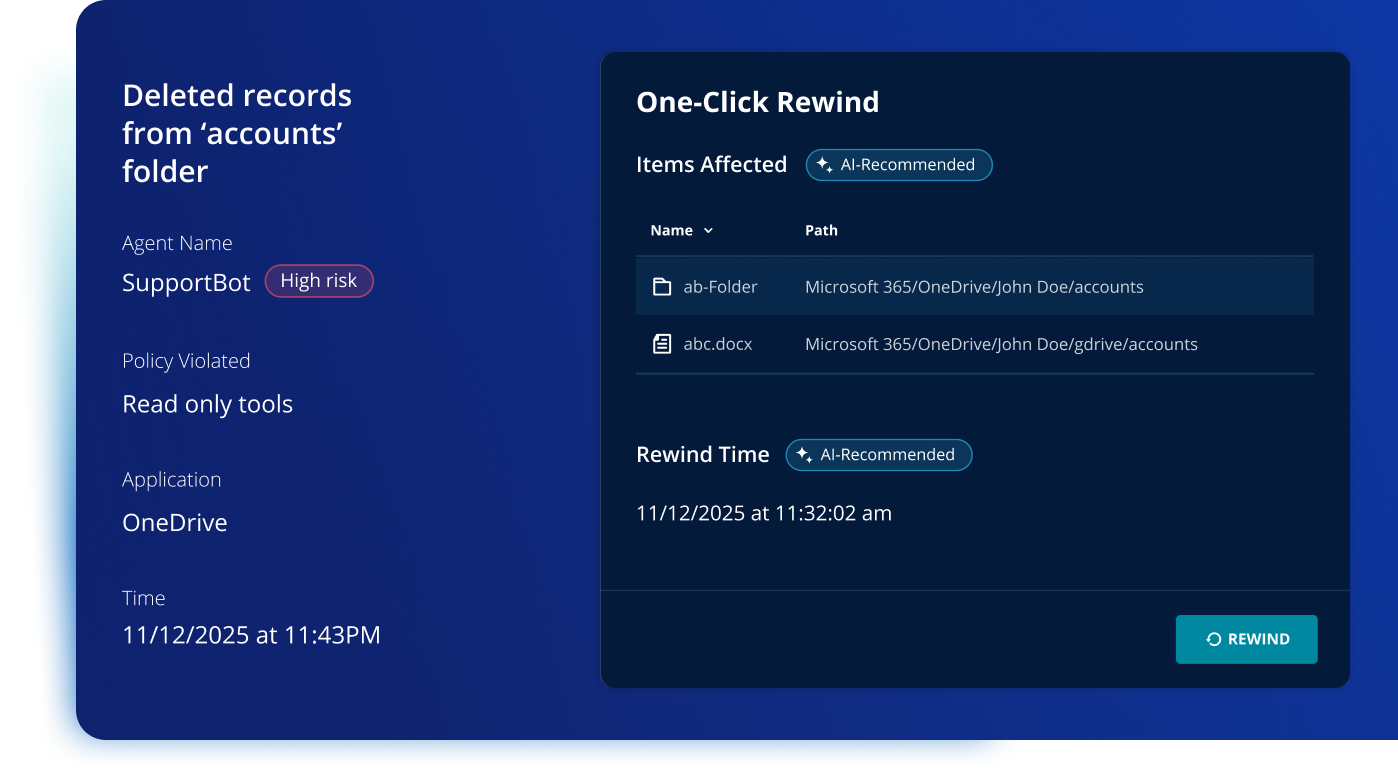
Rubrik Agent Cloud for Microsoft 365 Copilot
Adopt M365 Copilot with confidence. Monitor agent interactions, enforce guardrails, and instantly rewind your environment to remediate AI-driven data errors. Safeguarding Your Microsoft Copilot Deployment.
Monitor Agent Actions
Gain full visibility into agent interactions. Track access patterns in real time to prevent unauthorized M365 data exposure and maintain compliance.
Govern Agent Behavior
Set guardrails, monitor behavior, and enforce policies in real-time to keep Copilot studio agent actions in check.
Rewind Agent Errors
Instantly remediate agent errors by "rewinding" affected files to their last known good state without a full rollback.
EBOOK
Zero Trust Data Security for M365 with Rubrik and Microsoft
Addressing cyber attacks and other challenges require two shifts in approach. Download ebook to read more.

Add on Rubrik's Integration with Microsoft 365 Backup Storage
Add on the power of Microsoft 365 Backup Storage for the subset of groups or objects where you need an even lower Recovery Time Objective (RTO).1
Explore more of our resources
Rubrik for Microsoft 365
Watch Rubrik technology identify and protect sensitive Microsoft 365 application data using our OneDrive recovery capabilities.