Zero Trust Data Management™
Zero Trust Data Security Platform
Cyber-proof your enterprise data on physical systems, operating systems, virtual machines, databases, file systems, and containers with air-gapped, immutable, access-controlled backups.
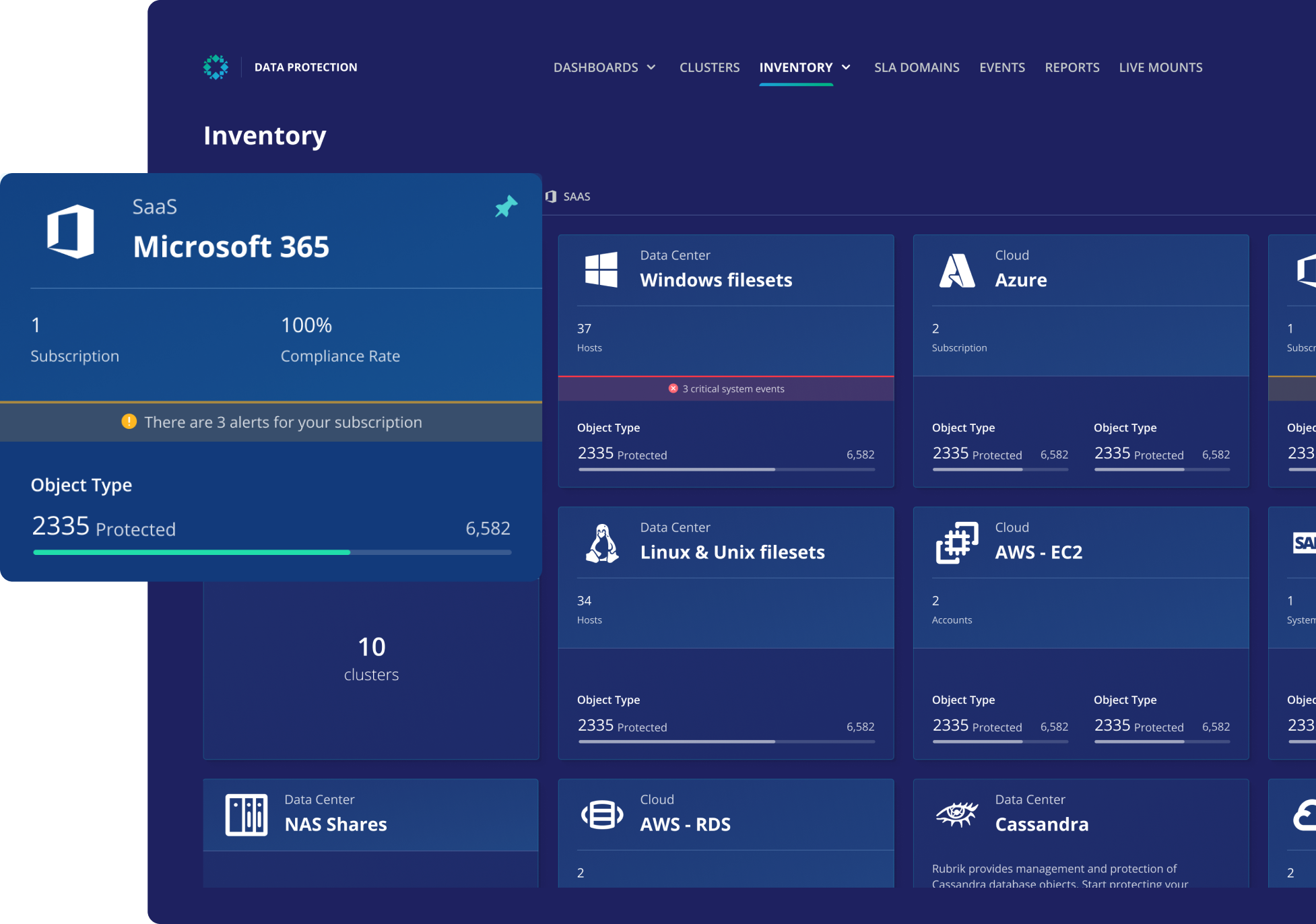
Data protection for hybrid and multi-cloud
Protect your enterprise data from cyber-attacks with an air-gapped, immutable file system that can’t be modified, deleted, or encrypted by hackers.
Prevent Encryption
Unify Protection
Accelerate Recovery
Definitive Guide to Zero Trust Data Security
Cyber threats are growing at an alarming rate. Learn how to protect backup data and minimize the impact of ransomware attacks with Zero Trust Data Security.
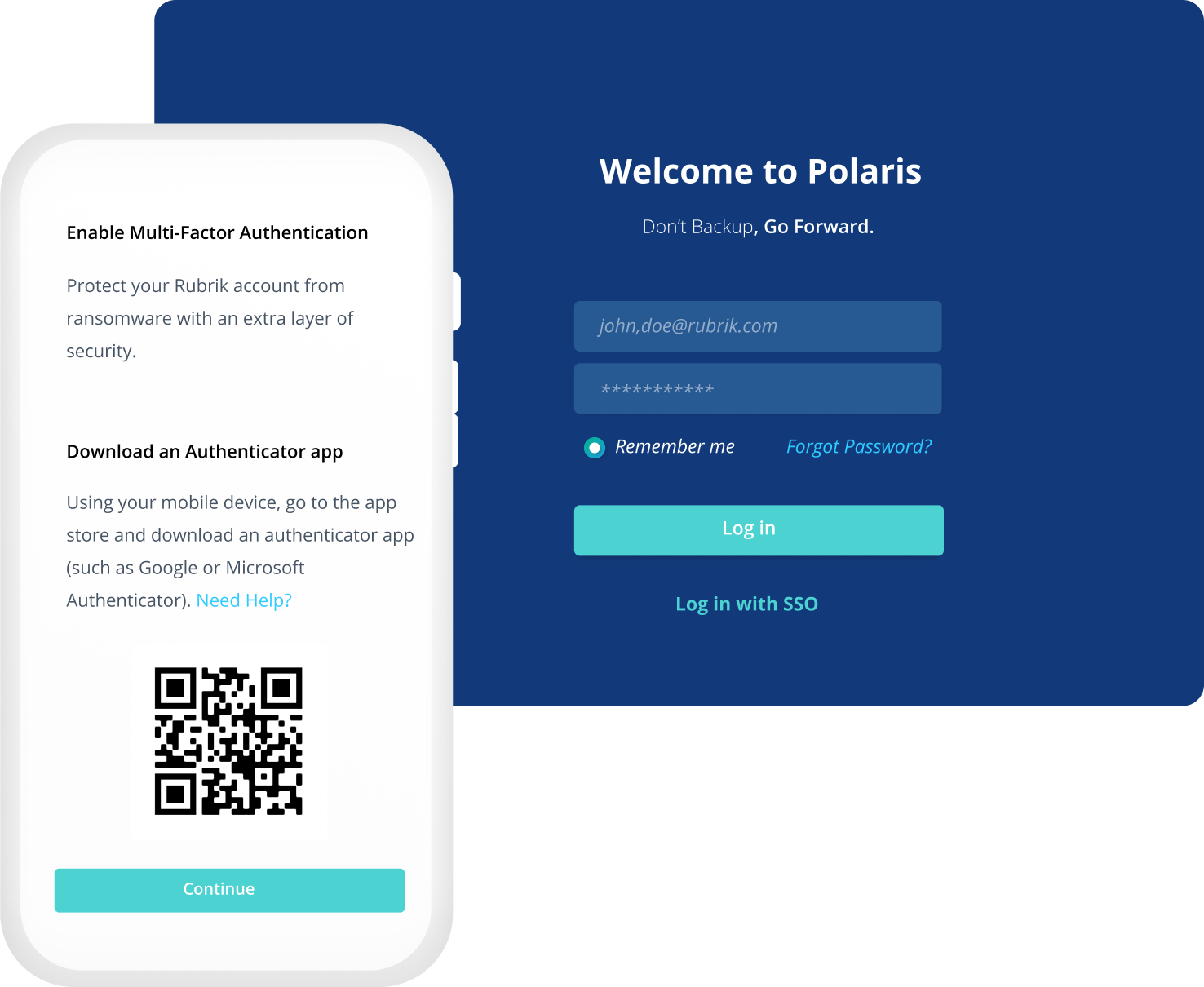
Keep your data protected
A logical air gap prevents attackers from discovering your backups while our append-only file system ensures backup data can't be encrypted. You can keep unauthorized users out with globally-enforced multi-factor authentication.
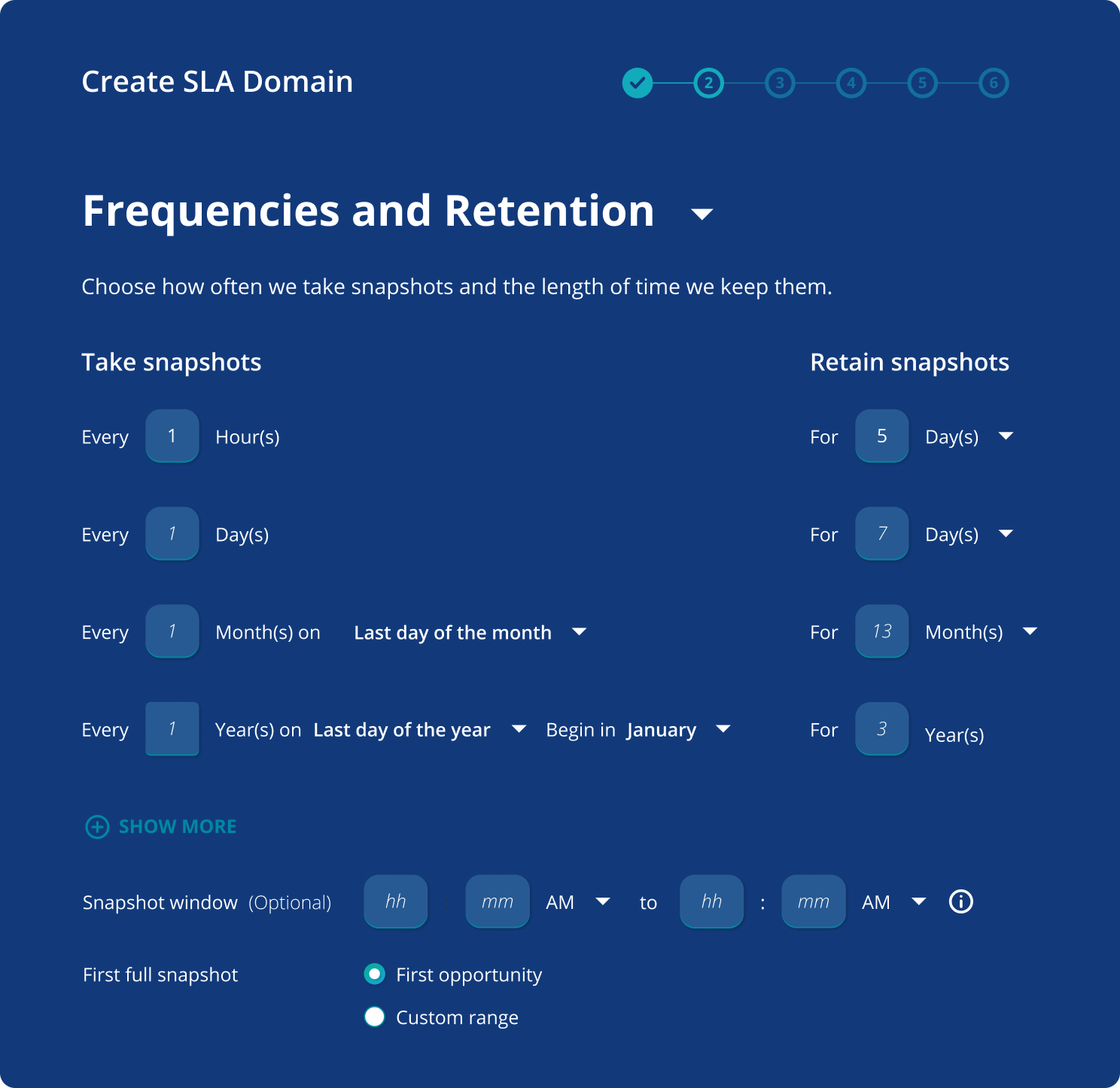
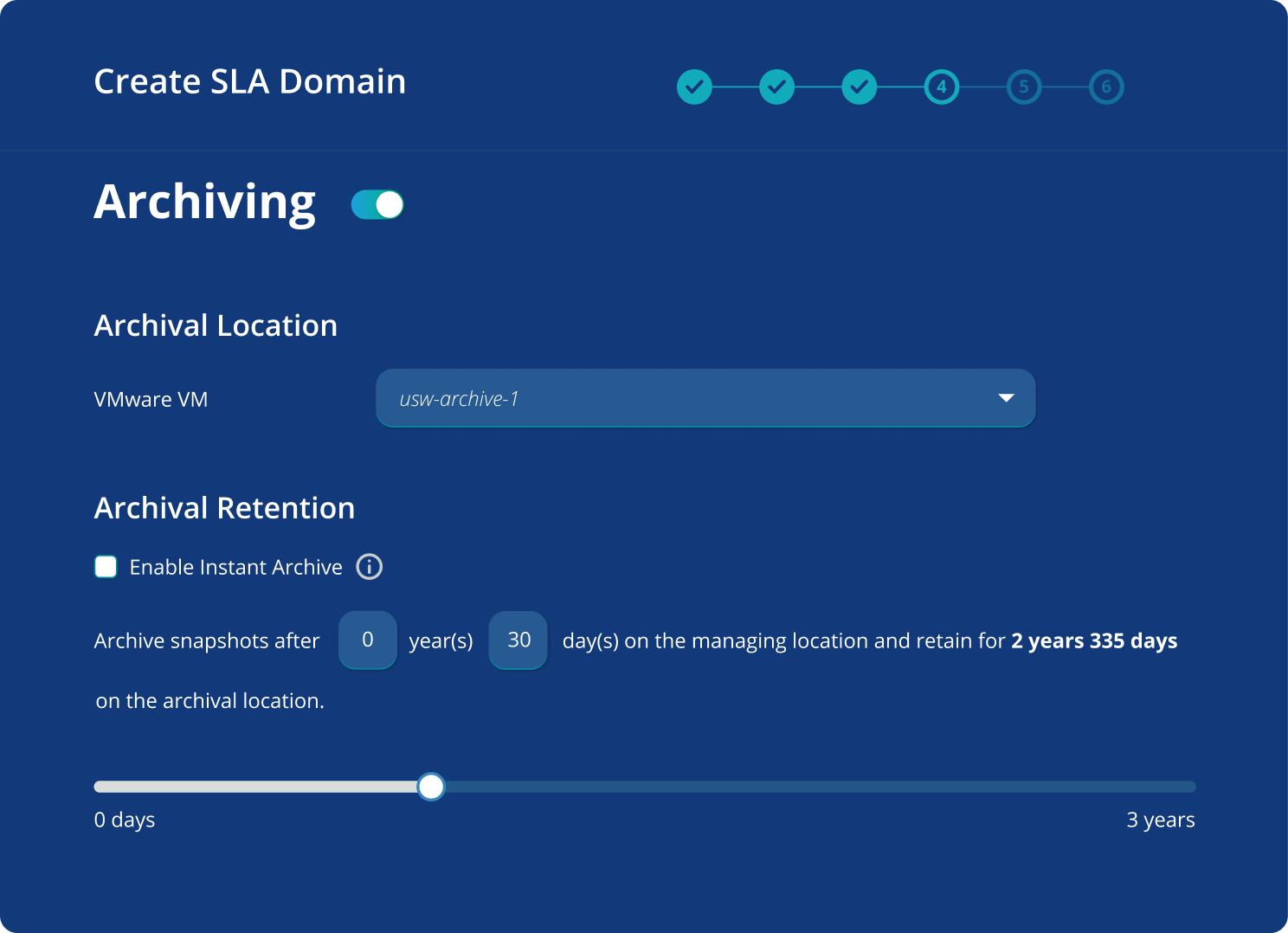
Automate your backup jobs
From backup frequency and retention to replication and archival, replace hundreds or thousands of backup jobs with just a few policies. Apply the same policies to all your workloads across on-premises and cloud.
Extend protection to the cloud
Archive your data to your public cloud provider’s blob storage service. Quickly access archived data with real-time predictive search.
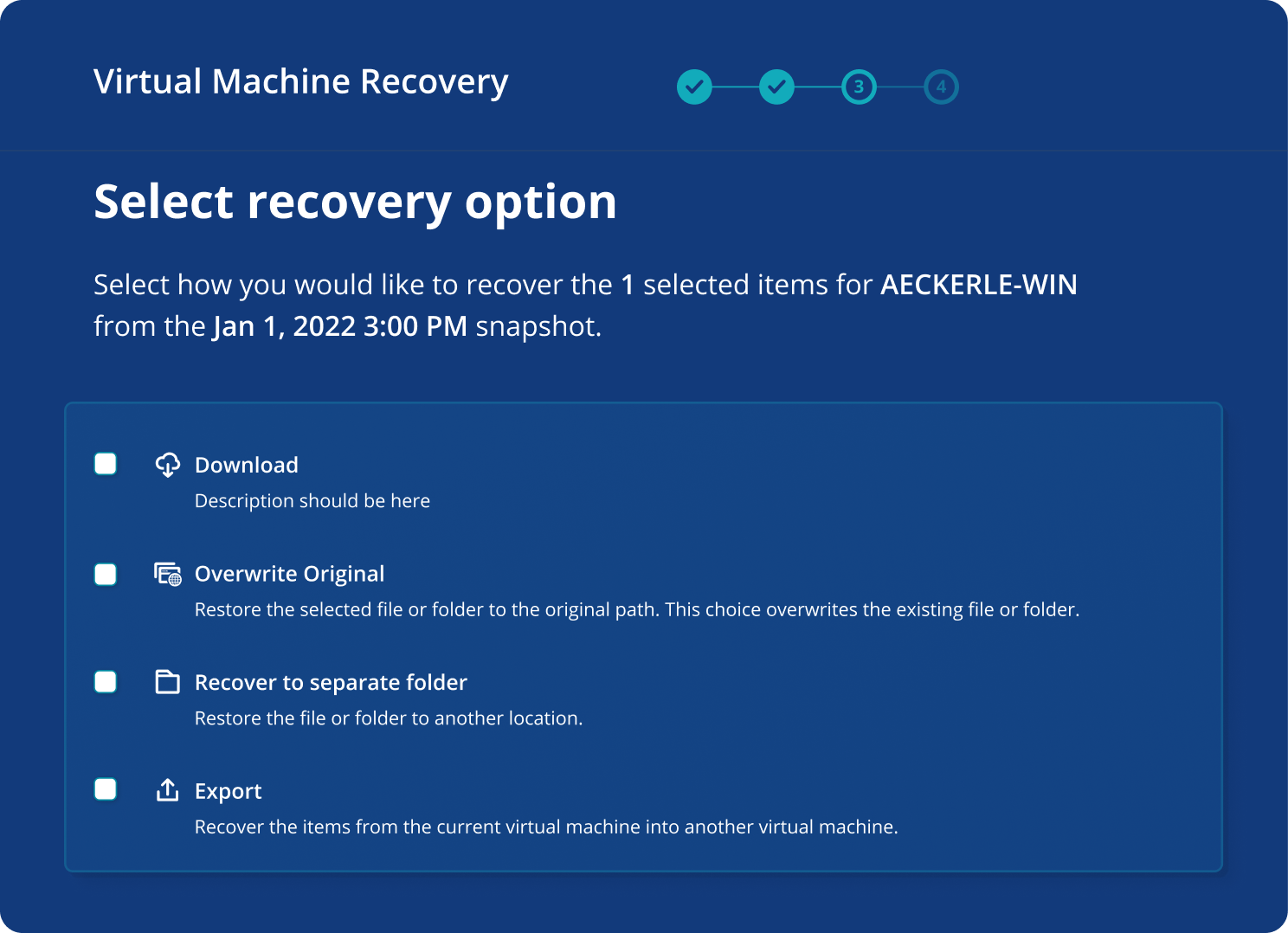
Recover with ease
Search across your entire environment, down to the file level, and select the right point in time to recover. Reduce recovery time from days and weeks to hours or less.
Zero Trust Data Security for Dummies
Discover how a Zero Trust Data Security architecture can improve your security posture and fortify your defenses against modern cyber threats.

Warren CAT Machinery & Rubrik: Securing Critical Data and Boosting DR Preparedness
Warren CAT saw the need to elevate their Zero Trust Data Security posture to protect their organization and secure their data in the face of cyber threats.

5 Keys to Mitigating Data Risk
Learn 5 tips to help you protect your data, minimize sensitive data exposure, and recover quickly in the event of ransomware.
Intro to Rubrik Security Cloud
See the Rubrik platform in action! It monitors the health of your critical data and helps you restore your business after a cyberattack.


