Prepare for the crisis you haven't met yet with Preemptive Recovery Engine™
Continuous scanning. Pre-computed clean states. Automated recovery orchestration. All before you need it.
The prevention myth is shattered
AI-powered attacks chain zero-days autonomously and escalate privileges in seconds. Prevention is futile. And recovery itself is broken: traditional approaches force teams to investigate during crisis, delaying recovery by weeks while costs mount.
The World's Only Preemptive Recovery Engine
What if recovery could start BEFORE a cyberattack hits?
Rubrik's Preemptive Recovery Engine performs the necessary prework to identify clean recovery points—before a cyberattack occurs.
The result: fastest cyber RTO.
Complete cyber resilience
A unified platform built to secure data, protect identity, neutralize threats, and preserve business continuity against AI-powered cyber threats.
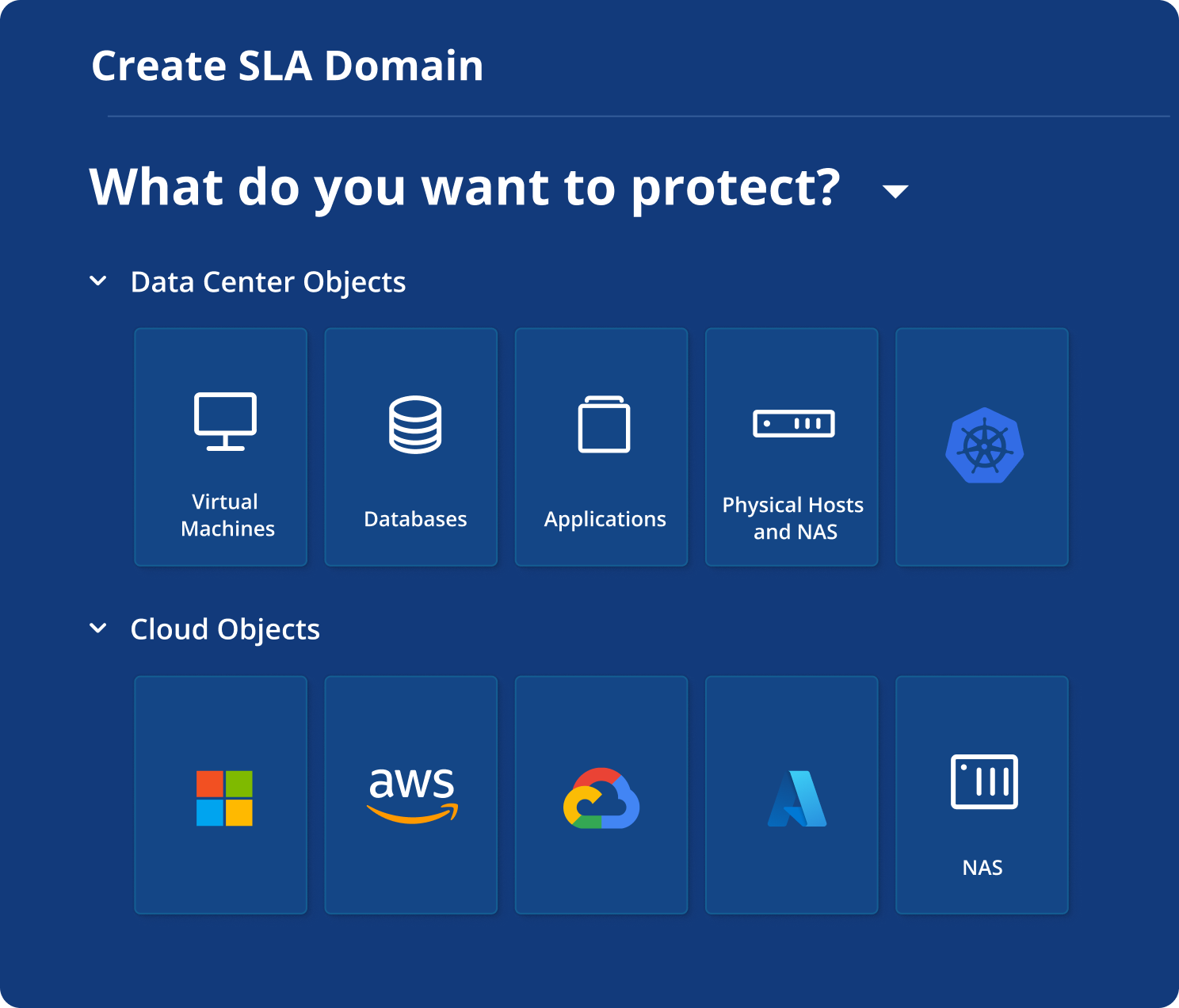
Secure your data (and future)
Unified data and identity resilience
90% of breaches exploit identity. Rubrik combines data and identity resilience, monitoring user-data access to detect drift, remove persistence, and fast-track recovery.
Complete resilience for the cloud
Rubrik delivers immutable backups with anomaly and threat detection, while cutting cloud TCO by up to 30%.
Accelerating AI from pilot to production
Rubrik Agent Cloud monitors, governs, and remediates AI agent behavior so you can move from pilot to production with confidence.
Achieve the fastest cyber RTO with the only Preemptive Recovery Engine
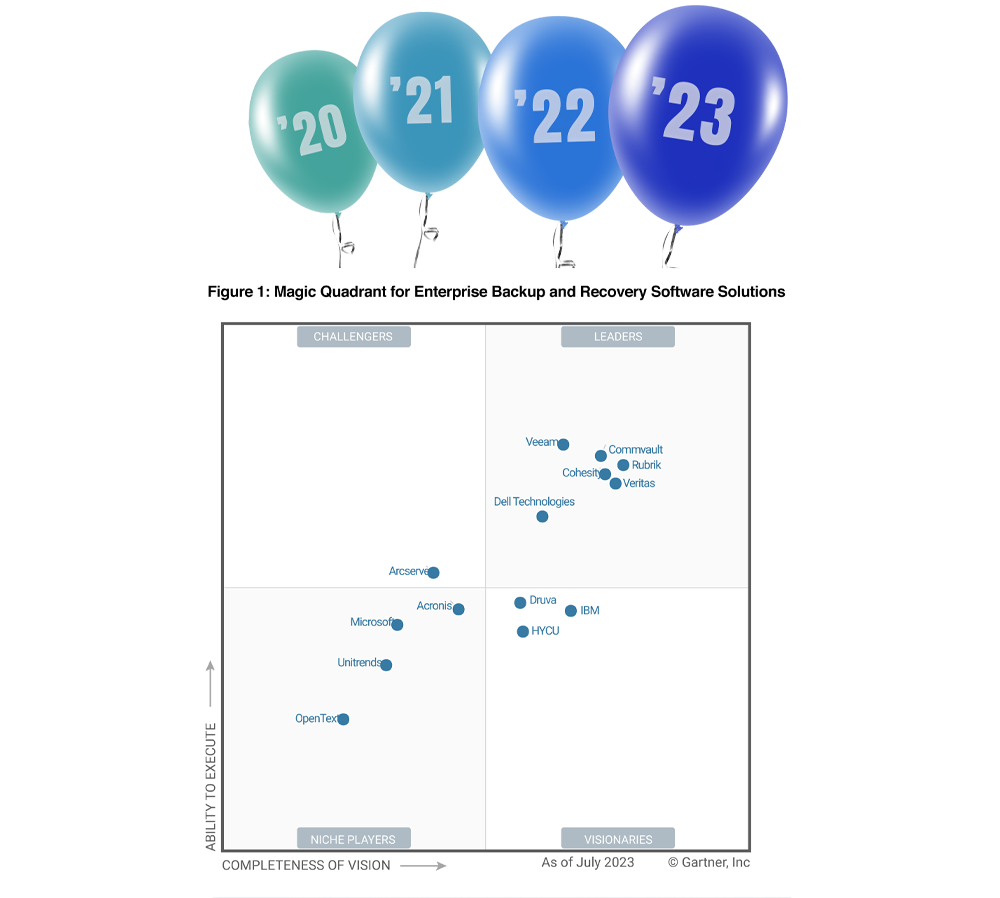
Rubrik: Four times a Leader and four times furthest in vision
For the 4th consecutive time, Rubrik has been named a Leader and the furthest in vision in the 2023 Gartner® Magic Quadrant™ for Enterprise Backup and Recovery Software Solutions.
Leading the way in cyber resilience
Proven Resilience
Hundreds of Cyberattacks. Fast Cyber RTO, when it matters most. Rubrik Ransomware Response Team support—24/7.
First of Its Kind
Anomaly Detection. Threat Monitoring. Threat Hunting. Sensitive Data Discovery. Natively built-in. End-to-end cyber recovery platform.
Undisputed Leadership
Gartner MQ Leader, Positioned Furthest in Vision for Backup and Recovery for five consecutive years.
Trusted by more than 6,000 organizations

"Rubrik equips us to search for security issues, helping us keep a clean data set for fast and secure data recovery that protects our reputation for dependable, trustworthy services."
-Duane Hopkins, Senior Manager of Cyber Security, Carhartt

When Your Data is Secure, Your Business Becomes Unstoppable
See how Rubrik Security Cloud:
-
Keeps data resilient against cyber threats
-
Monitors backup data for suspicious changes
-
Automatically brings applications back online
-
…and more
*Disclaimer: Any unreleased services or features referenced in this document are not currently available and may not be made generally available on time or at all, as may be determined in our sole discretion. Any such referenced services or features do not represent promises to deliver, commitments, or obligations of Rubrik, Inc. and may not be incorporated into any contract. Customers should make their purchase decisions based upon services and features that are currently generally available.