Agentic AI
Meet Ruby, Your New AI Teammate
Specializing in backup and recovery operations.
You Can’t Clone Your Best Engineers. So We Built You a New One.
Agentic Ruby
Designed to handle tedious work and routine operations—that drain your time and resources—so you can focus on what matters.
Works 24/7
Monitors failures, performs root cause analysis, and suggests remediation and recovery plans—ready to execute with your permission.
Operates within Guardrails
Choose your operating model: advisory mode for recommendations that wait for approval, or pre-approved actions within strict boundaries..
2025 Gartner® Magic Quadrant™ for Backup and Data Protection Platforms.
Read the Gartner 2025 Magic Quadrant report for an in‑depth analysis of the enterprise backup and data protection market, and why Rubrik is positioned as a Leader for the 6th consecutive year.

Ruby in Action
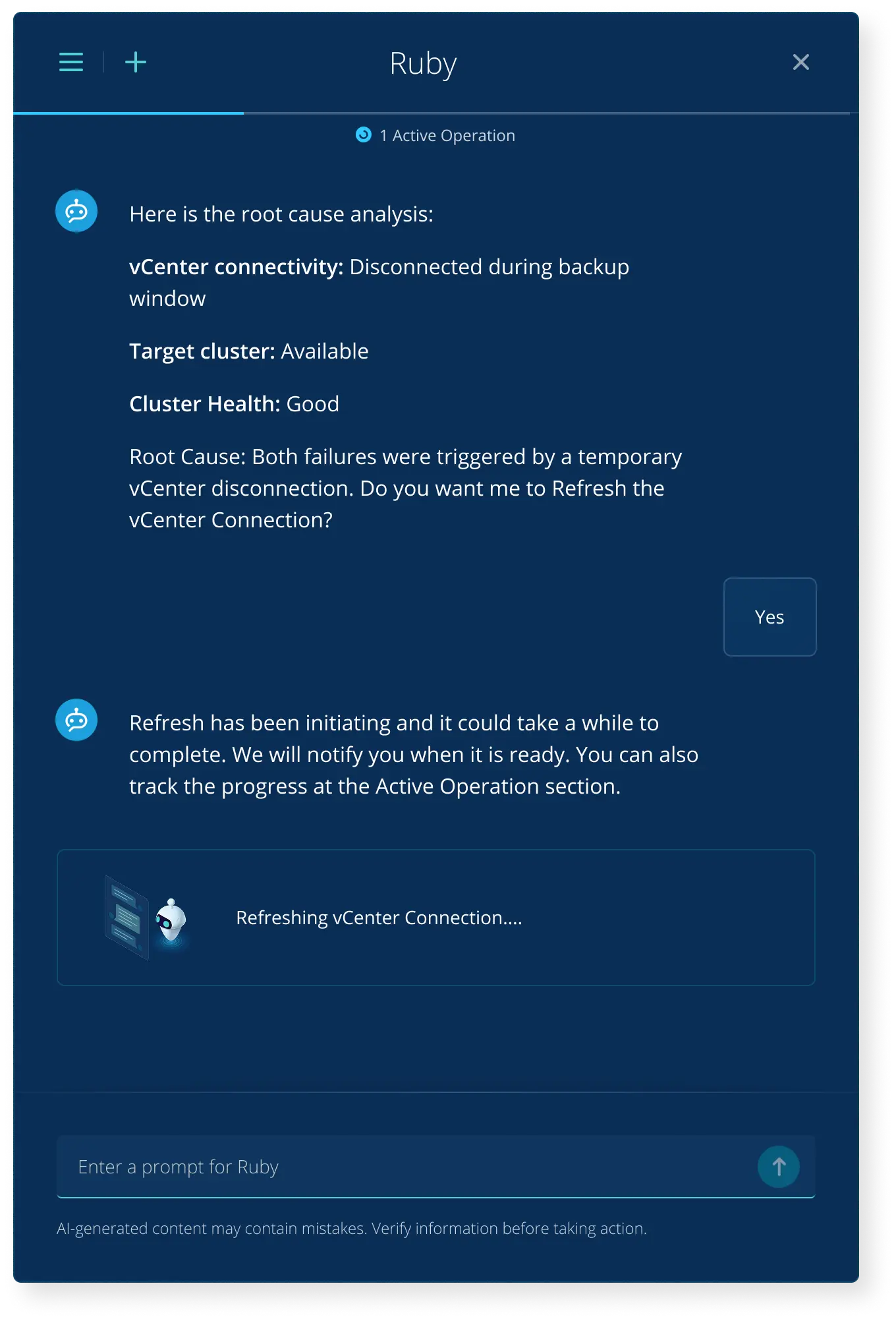
Troubleshooting
A backup fails. Usually, this requires hours of cross-referencing error codes, checking network connectivity, and stitching together signals from different clusters.
The Ruby Workflow:
Diagnosis: Ruby detects the failure and correlates signals. "vCenter is disconnected."
Recommendation: "Refresh connection and restart job."
Action: Upon your approval, Ruby executes the fix and validates the next backup.
Result: Instant Resolution.
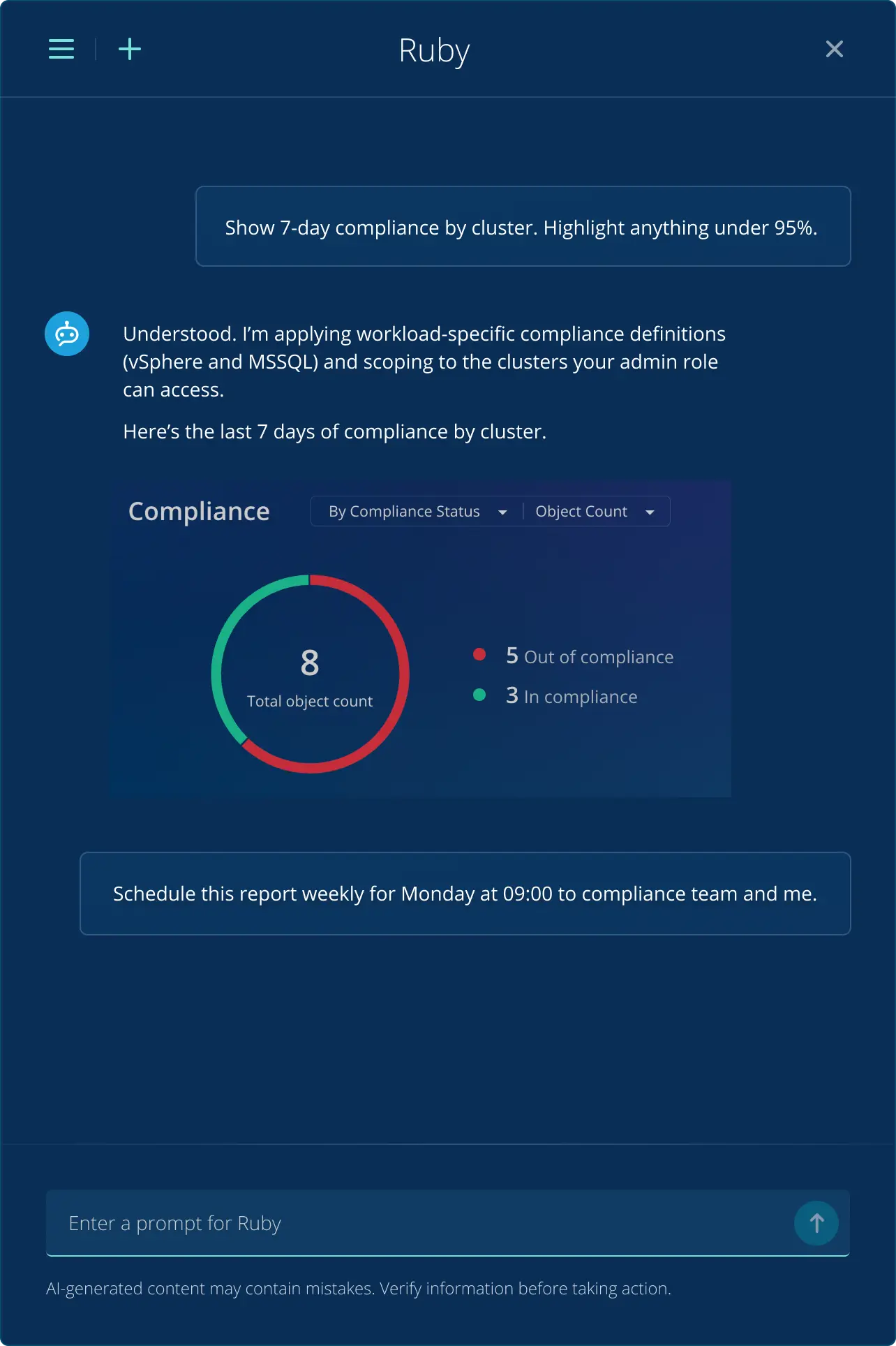
Reporting
The constant questions. "Why is storage spiking?", "Are we audit-ready?" Answering these requires merging data from three different consoles and writing custom scripts.
The Ruby Workflow:
The Prompt: "Show me a 7-day compliance report for all financial clusters. Highlight anything under 95%."
Analysis: Ruby maps the data, respects your specific access permissions, and provides a visual summary.
Result: Immediate Visibility.
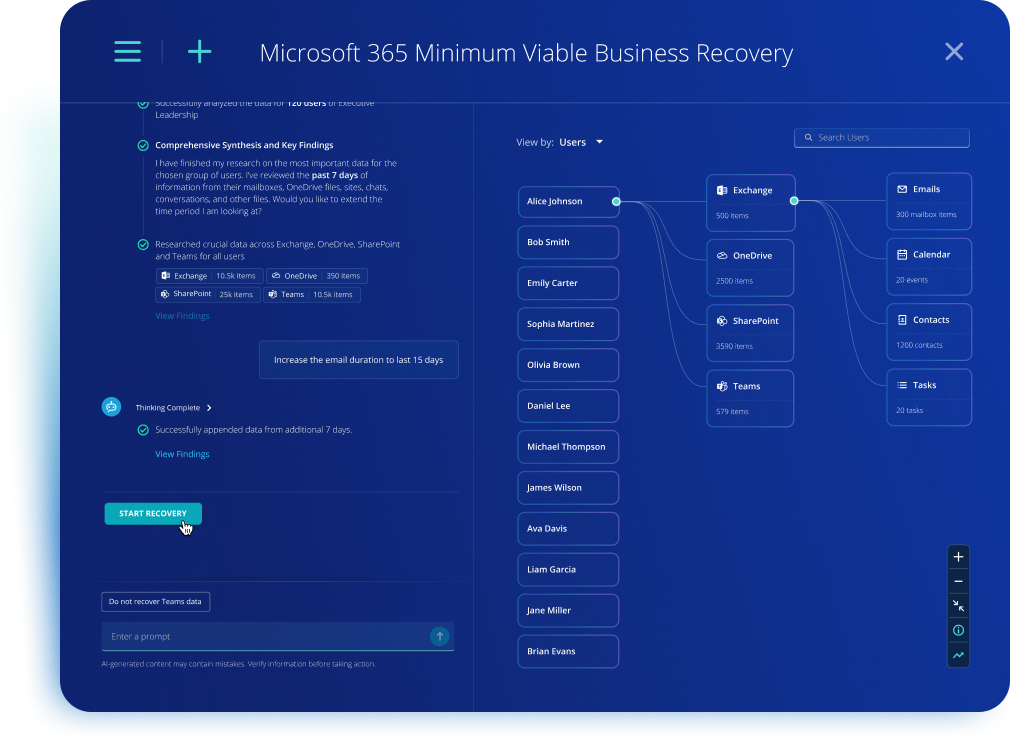
Recovery
In a crisis, say M365 outage, you can't recover everything at once. Deciding who comes back first—and finding their specific data across Exchange, OneDrive, and Teams—is high-pressure manual guesswork.
The Ruby Workflow:
The Strategy: Define your critical core (say executive leadership) as the Minimum Viable Company.
The Prompt: "Recover my Minimum Viable Company"
Analysis: Ruby builds a Context Map of recent activity (emails, calendars, active files) to identify exactly what is needed to be operational.
Action: Upon approval, it recovers the critical core immediately while the full petabyte-scale restore runs in the background.
Result: Surgical Business Resilience

Cyber Recovery Blueprint
Find a clean backup and recover your business with speed and certainty.

Building a Business Case for Cyber Resilience
Gain the practical tools and proven strategies needed to build a persuasive business case that shifts the conversation from abstract technical risks to measurable ROI.
Rubrik AI
Chat with Rubrik Ruby AI and learn how artificial intelligence can help you respond to (and recover from) a cybersecurity incident.

