Remember when Tom Cruise hung upside down from the ceiling in Mission Impossible and tried to steal data from a computer housed in a top-secret vault at CIA headquarters? From the perspective of today, we might wonder why all the crawling through the air ducts and risking his neck was necessary. Couldn’t he just hack the machine? No, because that CIA system was air-gapped. It was a freestanding computer that was not attached to any sort of network. If you wanted to use it, you had to be in that highly secured room. At least, that’s how the thinking went.
It’s easy to make fun of Hollywood and its excesses, but the film did reflect the predominant view at the time that the best security came from putting air between a system and anyone or anything trying to reach it. Things have changed, though. Air gaps still exist. Some organizations absolutely require them, but the practical realities of implementing and sustaining an air gap have grown quite a bit more difficult over the last two decades. To understand why air gaps are still important, it’s worth taking a moment to define the concept and explore what’s working well with them and what isn’t.
What is an Air Gap?
An air gap is a security measure that physically isolates a system or data storage from external networks to prevent unauthorized access and cyber threats. Air gap backups provide a last line of defense against data loss by keeping critical information separate from network-connected environments. Businesses use air-gapped backups to protect data from cyberattacks, system failures, or disasters such as fires or floods. These backups are typically stored in a secure off-site location and can be used to restore data in case of corruption, hardware failure, or ransomware attacks
Air Gap Backups for Business
As the world moves increasingly online, air gap backups provide a last line of defense against data loss. Businesses of all sizes can benefit from air gap backups, which protect data from being destroyed, accessed, or manipulated in the event of a network intrusion or system failure.
Air gap backups are typically stored in a secure location off-site from the business, such as in a secure server facility. Air gap backups can be used to restore data in the event of a disaster, such as a fire or flood, or if data is lost or corrupted due to a software glitch, hardware failure or ransomware attack.
There are several things to keep in mind when implementing air gapped backups for business:
Air gap backups should be stored in a secure location that is not accessible to unauthorized personnel.
Air gap backups should be updated regularly, typically daily or weekly.
Air gap backups should be tested periodically to ensure that they can be used to restore data in the event of a disaster.
Air gap backups should be encrypted to protect sensitive data from being accessed by unauthorized personnel.
Implementing air gap backups can be a challenge for businesses, as it requires a high level of security and planning. However, air gap backups provide a critical layer of data protection against all forms of data loss, and can help businesses recover from a wide range of disaster recovery situations.
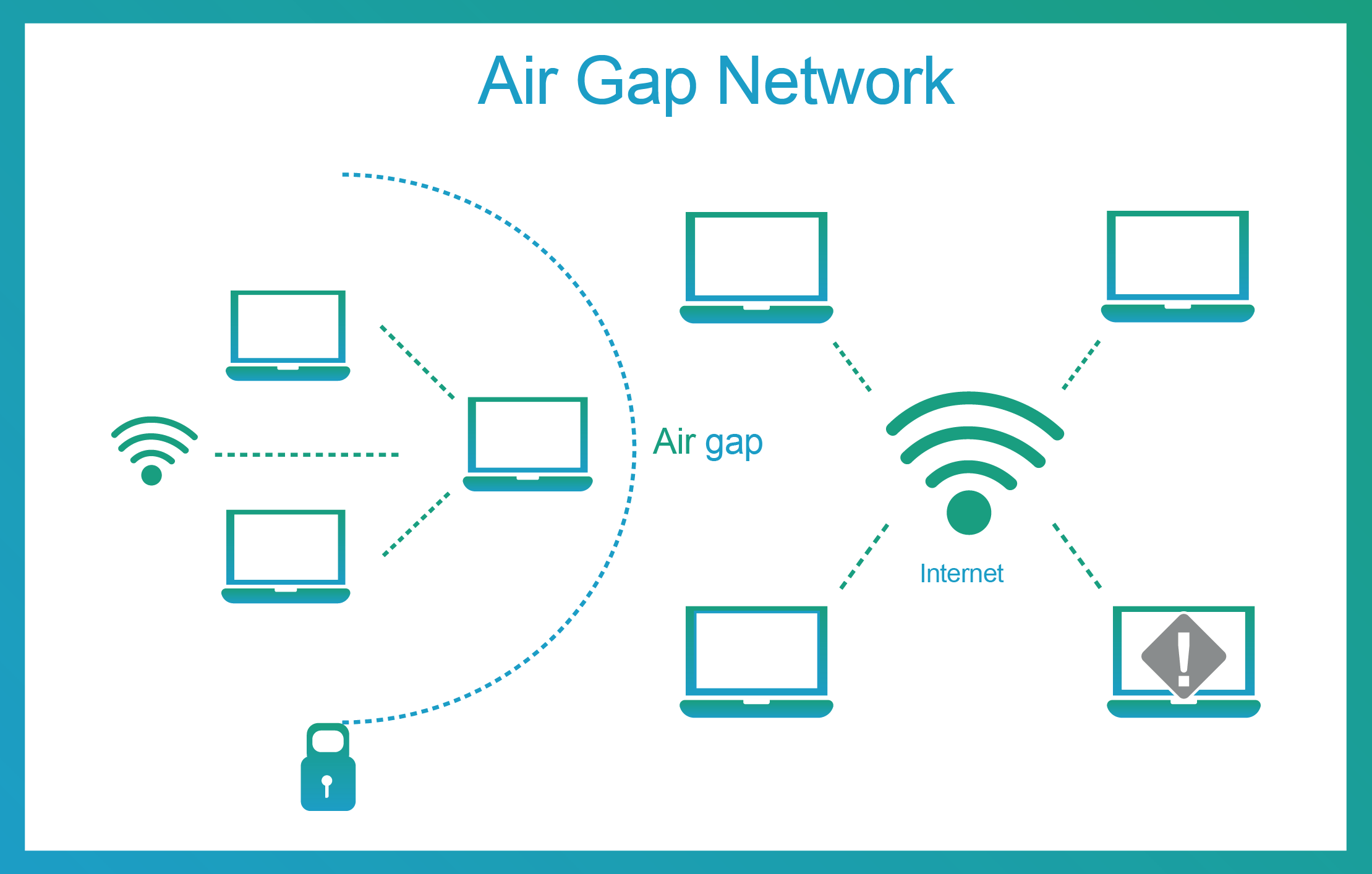
Types of air gaps
There are many variations on the air gap concept. At a high level, three main types are the most common:
The total physical air gap—This is the salt mine type, which involves locking digital assets in a completely isolated physical environment, separated from any network-connected systems. A digital asset in a total physical air gap has no network connections. If anyone wants to get data from it or put data onto it, they must physically go to it, a process that usually involves going through physical security barriers.
Segregated in the same environment—An air gap can be achieved by simply disconnecting a device from a network. One could have two servers on the same rack, for instance, but still air-gapped away from each other because one is not plugged into the network.
Logical air gap—A logical air gap refers to the segregation and protection of a network-connected digital asset by means of logical processes. For example, through encryption and hashing, coupled with role-based access controls, it is possible to achieve the same security outcomes that are available through a physical air gap. Even if someone can access the digital asset, the asset cannot be understood, stolen, or modified.
Criticisms of Air Gaps & Air Gap Backup Data Protection
One popular school of thought in today’s cybersecurity circles holds that there is simply no such thing as an air gap any longer. While this may sound like a flippant generalization, there is some truth to it. One issue is the pervasiveness of Internet connectivity today. With literally billions of devices connected to the Internet, and connections existing between devices, it is likely that a system that purports to be air-gapped actually has an Internet connection that no one knows about.
In fact, when organizations deploy device scanning tools to create an inventory of all their network connected devices, they invariably discover equipment that no one knew even existed, much less had a network connection. When one factors wireless network connections into this analysis, it becomes possible to imagine even more lapses in air gap design. A system may be physically separate, but still connected over the very air that is supposed to be forming a total barrier to access. Furthermore, hackers can now use highly sophisticated wireless “sniffing” technologies to glean data from a system that is otherwise physically isolated.
Ransomware Recovery for Dummies
Don’t Panic: Easy Steps to Ransomware Recovery
Challenges of air gaps
Air gaps are not easy to set up and sustain. In addition to being threatened by accidental connections or enterprising hackers, air gaps suffer from a variety of human-centric risks. Input/Output is the root issue. Air gap or not, users typically need to add, modify, or download data from the system. This is true for backups as well as production systems. Thus, most traditional air gaps involve what is popularly known as a “sneakernet,” a physical method of transferring data, e.g., a Wi-Fi dongle or USB port.
At this point, human nature takes over. Even well-intentioned users will accidentally leave doors unlocked or USB ports unguarded. They may get lazy and neglect to follow security procedures. One worrisome example of this risk occurs on merchant ships and naval vessels, whose mechanical control and navigation systems are air-gapped because, well, they’re on a ship and generally not connected to the Internet (though even that is starting to change.) Once a ship is docked, however, a malicious actor can gain access to the ship and use a USB stick to insert malware into the system. When a ship undergoes maintenance, and hundreds of semi- or non-vetted workers are aboard the vessel while the regular crew is away, it’s easy to see how an air gap will fall apart.
A supply chain attack can penetrate air-gapped systems through the software that runs them. This is how the unattributed attacker was able to place malware into an Iranian nuclear site, even though the place was underground, completely cut off from the outside world and guarded by soldiers. By planting the Stuxnet virus into a command-and-control system update, the attacker got through the air gap and destroyed centrifuges that were refining uranium.
Social engineering and insider attacks can also get past air gaps. Hackers who need physical access to a site in order to penetrate an air-gapped environment are usually clever enough to fake their way in by impersonating real employees or other ruses. (Look at Tom Cruise! He came in with the fire department.) Insiders are a persistent threat to air gaps as well, unpleasant as it may be to contemplate.
Encryption of data at rest is a good countermeasure to apply in conjunction with air-gapping for these reasons. An attacker will probably gain access to the air-gapped system if they truly want to break in. The best practice is to ensure that whatever data they can steal will be completely useless to them.
Buyers Guide
The Smart Buyer’s Guide to Ransomware Protection & Recovery
Conclusion: Putting air gaps into viable cyber defense context
The best practice today is to be realistic about air gaps. They can work, and indeed they can be very effective in the right circumstances as part of a backup and recovery strategy. It’s essential, though, not to adopt a simplistic mindset and think “It’s air-gapped, so therefore it’s secure.” This is simply no longer true.
Instead, it makes sense to think carefully about desired outcomes, risks and vulnerabilities for a specific air gap use case. For example, if the goal is to secure backups, then encryption is critical for a viable air gap. Also, a logical air gap may be the best solution. A physical separation may not be required. Implemented correctly, an air gap provides a strong layer of cyber defense.