Compliance & Risk Mitigation
Mitigate data risk
Minimize business impact of ransomware attacks and facilitate compliance with ever-increasing data privacy regulation.
Protect Your Business-Critical Data
With ransomware attacks on the rise and increasing data privacy breaches, you need tools that help prevent revenue, reputational, and data loss. With Rubrik, deliver fast, reliable recoveries and discover sensitive information hiding in your unstructured backup data.
Minimize Downtime
Rubrik backups can't be compromised by ransomware. Easily restore to the most recent clean version of your data.
Identify Data Exposure
Instant visibility into high-risk data, such as over permissioned access or sensitive data stored in unauthorized locations.
Encrypt End-to-end
All data read by, stored in, or replicated with Rubrik’s software platform is encrypted, whether on-premises or in the cloud.
5 Keys to Mitigating Data Risk
Learn 5 tips to help you protect your data, minimize sensitive data exposure, and recover quickly in the event of ransomware.
Secure backups
Rubrik natively stores all data in an immutable format with encryption and access controls to ensure data is kept readily accessible.
Ransomware impact assessment
Rubrik automatically diagnoses scope of attack impact and provides a clear view into what data was impacted and where it resides. With modern ransomware threatening to publicly disclose stolen data, you can now identify if certain personally identifiable information (PII) and protected health information (PHI) was exposed.
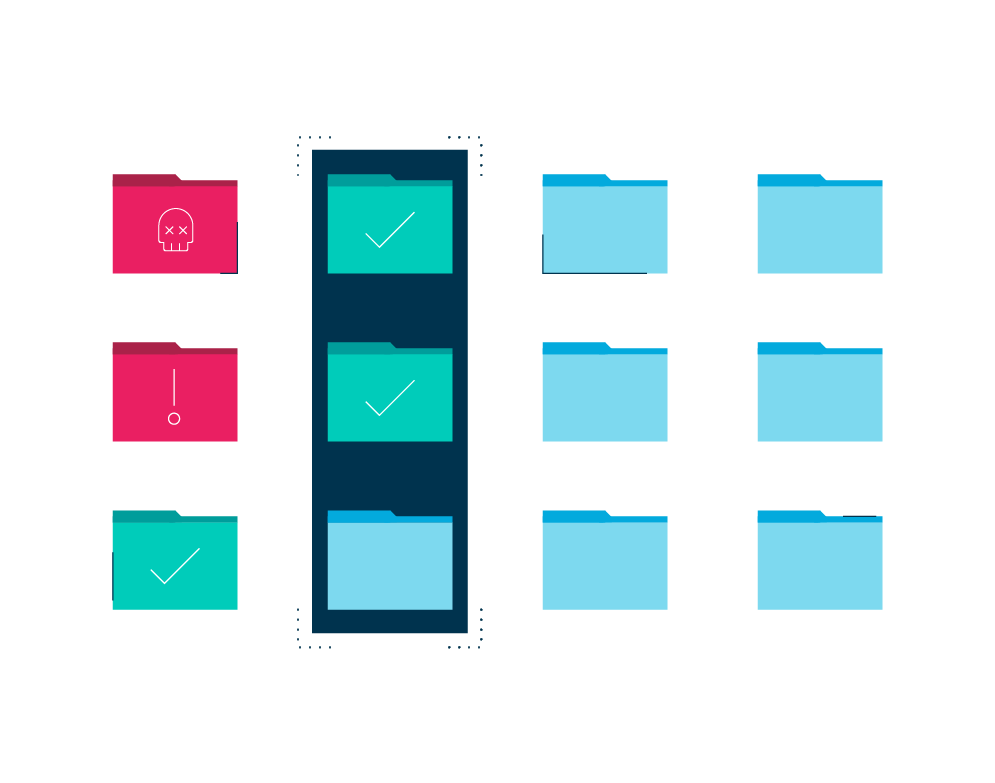
Audit and regulatory compliance
Rubrik automatically discovers, classifies, and reports on where certain types of sensitive data reside to help comply with regulations such as PCI/DSS, SOX, HIPAA, and data privacy requirements such as GDPR.

Stronger access controls
Global access or “open shares” is often the biggest risk for an attack or theft of certain types of sensitive data. Gain visibility into who has access to sensitive data. With greater awareness over user permissions, you can reduce the risk of data breach.

Rubrik Zero Labs
Discover why organizations remain optimistic about security despite the realities, and explore trusted methods to enhance your data security.

Ready to get started?
Get a personalized demo of the Rubrik Zero Trust Data Security platform.