Mass recovery
Rapidly recover your systems
Restore business operations quickly by recovering apps, files, or users at scale.
Bring your business back online
When a disaster or ransomware attack strikes, a simple yet scalable path to recover data can help avoid costly interruptions.
Ensure business continuity with a secure recovery of your data and applications that meets your business' recovery time objectives.
Minimal Downtime
Reliable Recovery
Flexible operations
2025 Gartner® Magic Quadrant™ for Backup and Data Protection Platforms.
Read the Gartner 2025 Magic Quadrant report for an in‑depth analysis of the enterprise backup and data protection market, and why Rubrik is positioned as a Leader for the 6th consecutive year.

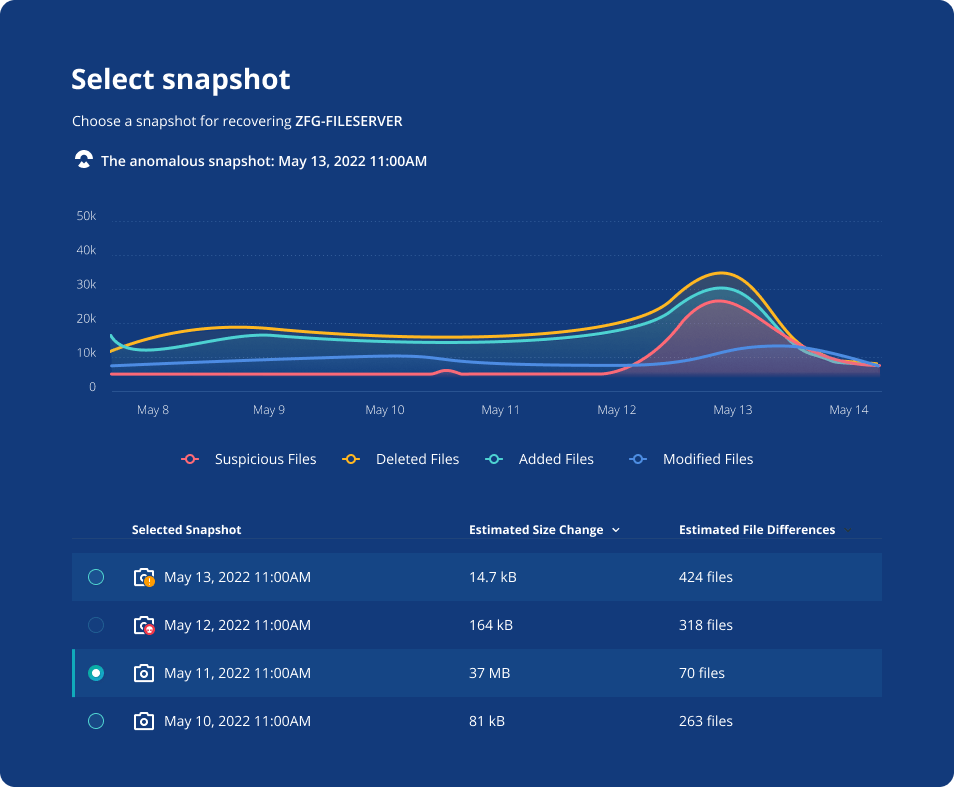
Recover to a suggested snapshot
No more spending time looking for a recovery point. When hit by ransomware, recover all your data from the latest clean snapshot— suggested by machine learning.
Execute smooth mass recovery operations without key-person dependency or specialized skills.

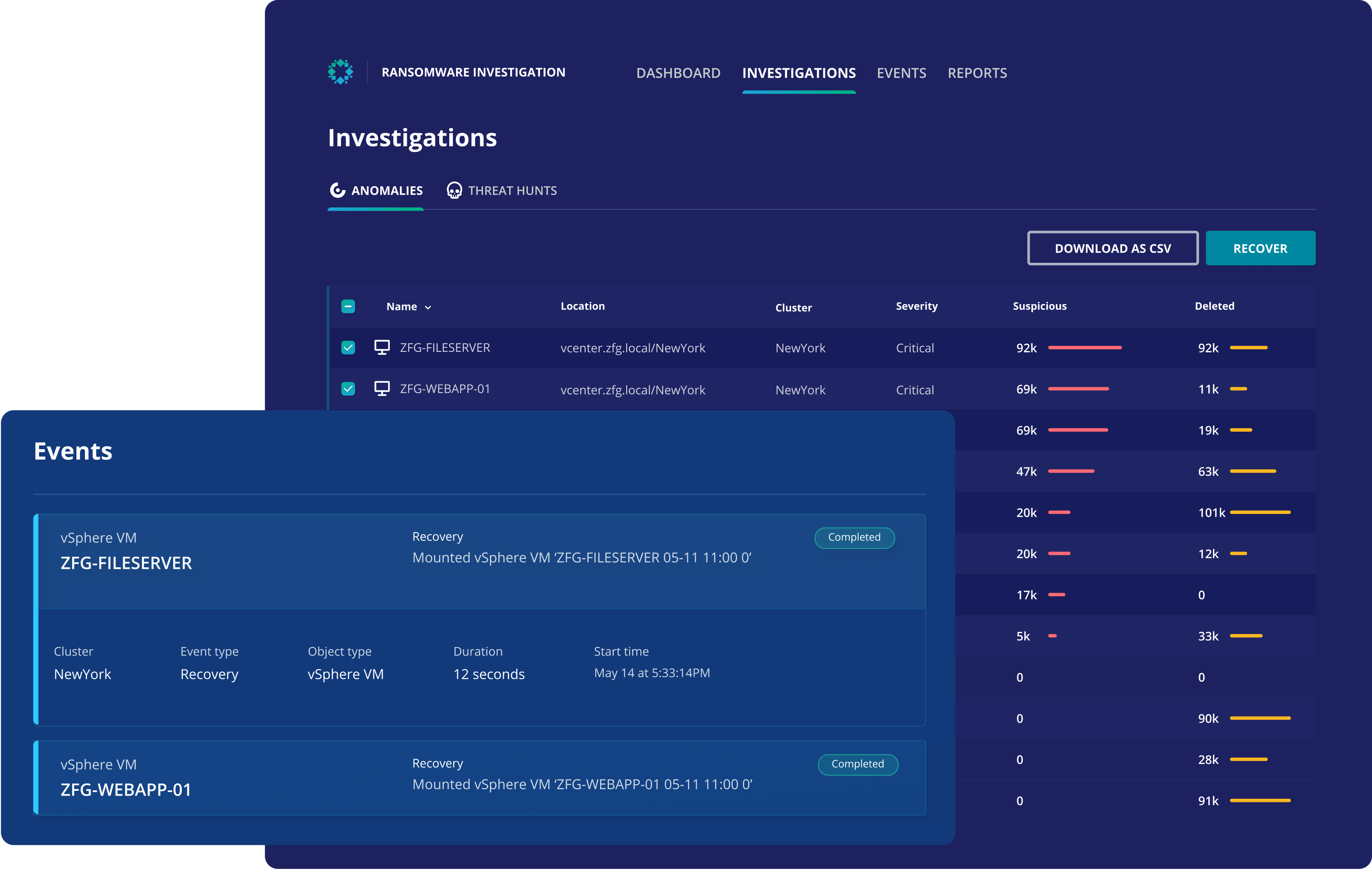
Easily identify a clean snapshot
Select the last known good copy by analyzing snapshots exhibiting anomalous behavior and signs of encryption.
Ransomware Investigation provides guidance on when, where, and how systems are infected so you can safely recover your data.
5 Keys to Mitigating Data Risk
Learn 5 tips to help you protect your data, minimize sensitive data exposure, and recover quickly in the event of ransomware.
FLEXIBLE RECOVERY
Select your recovery approach
To restore business operations with near-zero downtime, you need the scale of mass recovery along with the flexibility to recover only what you need. Depending on the scope and impact of the attack, certain recovery techniques perform better in terms of speed and efficiency, helping you meet your business RTO objectives.
Surgical ransomware recovery
Instant application recovery
Storage outage recovery
Proactive recovery testing
Automated site recovery
whitepaper | White paper
Backup & Recovery Best Practices
Get prepared for the explosion of new non-traditional apps, the expanding remote workforce, as well as emerging ransomware threats in this new ebook.

blogpost | 15 min read | Jul 22, 2021
Recovering from the different types of Ransomware with Rubrik
There has been no shortage of ransomware headlines in 2021. While these attacks can shut down critical IT systems for extended periods, Rubrik has helped numerous customers quickly recover from ransomware events and get their businesses back up and running.
Ready to get started?
Get a personalized demo of the Rubrik Zero Trust Data Security platform.