Data security is not a new priority for enterprises. In earlier blog posts, we discussed the rising threat of ransomware and how a next-gen data management solution prevented a ransomware attack. Given the exponential growth of data and increasing trend in data breaches, it is imperatives that businesses apply the highest security standards to all their data.
However, the concept of security is often confounded in the context of data management. To clarify the important terms, components, and their implications for data security within enterprise backup and recovery, I sat down with Adam Goldberg, who leads product development for Rubrik’s security solutions. Adam comes from a security background with previous experience at the Department of Defense Federal Information Processing Standard (FIPS)
Federal Information Processing Standard (FIPS)
FIPS 140-2 is the National Institute of Standards and Technology (NIST) security standard used to accredit cryptographic modules. It is often a requirement for a product to be installed in a location where sensitive data is stored. The FIPS 140-2 standard extends far beyond the federal government. For example, financial and healthcare institutions collect, store, and transfer highly sensitive information that needs to be secured.
While FIPS 140-2 features four levels of security, only Level 1 and Level 2 are relevant to a backup and recovery data center appliance. Level 3 and Level 4 are only relevant for devices like Hardware Security Modules.
- Level 1: The first level of security – the cryptographic module should have at least one approved algorithm. No physical security mechanisms other than production-grade components.
- Level 2: Adds physical security to hardware components requiring features to show evidence of tampering, including coatings and seals that would be broken upon access.
The main differentiator between Level 1 and Level 2 is the tamper-evidence requirement of Level 2. Because of this requirement, FIPS 140-2 Level 2 encryption can only be obtained in a backup appliance via hardware. Rubrik employs Self-Encrypting Drives (SED) that are certified at FIPS 140-2 Level 2 due to their tamper-evident seals.
Common Criteria
The Common Criteria for Information Technology Security Evaluation is an international standard (ISO/IEC 15408) for computer security certification. Common Criteria is a security standard that has been agreed upon by 26 countries worldwide. Common Criteria certification is an important way for security-conscious industries and governments to keep their data safe. Common Criteria evaluation comes in different levels, known as Evaluation Assurance Levels (EAL), from 1 to 7. EAL1 indicates the most basic level and is the cheapest to implement and evaluate. EAL7 indicates the most stringent level and is expensive to evaluate.
NOTE: Higher EALs do not necessarily imply “better security.” They only indicate that the claimed security assurance of the TOE has been more extensively verified.
Rubrik is in process with Common Criteria at the EAL2+ level. The “+” indicates an augmentation on top of EAL2, namely the security development lifecycle certification.
Trusted Platform Module (TPM)
The FIPS 140-2 standard does not ensure how a key is stored, so a security-conscious data center administrator needs to know that their encryption keys are being stored securely. A Trusted Platform Module (TPM) is a piece of hardware that can be used to protect encryption keys stored on an appliance. In particular, it enforces that someone knows a disk password in order to change it. In order to mount a disk, it is required to present its password during boot. The TPM ensures that someone cannot compromise the system even if it has already been mounted.
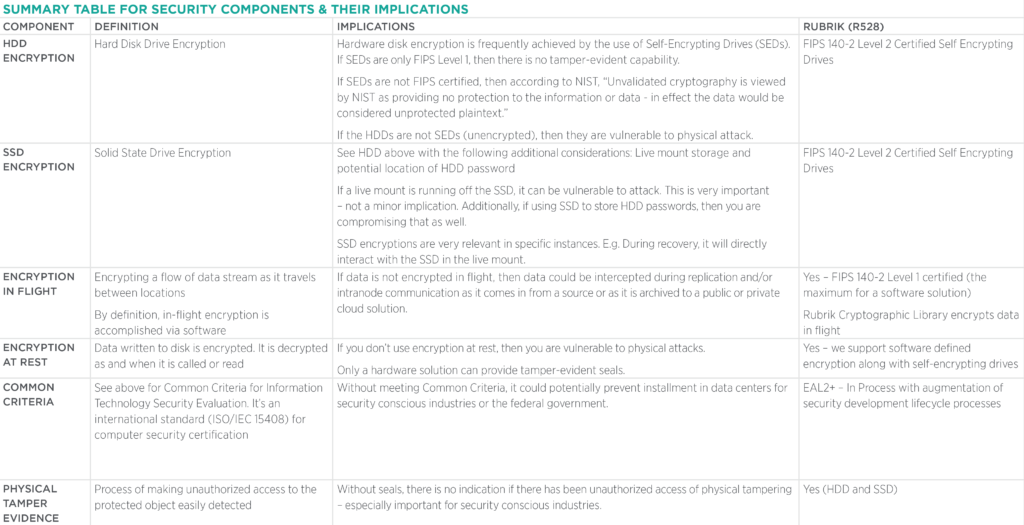
Important Components and Their Implications for Data Security
Other Key Definitions
Certified: Publicly available certificate of validation
Compliant: Supposedly adheres to the guidelines at a minimum level
Cryptographic modules: a set of hardware, software, or a combination that implements cryptographic functions, such as encryption or other authentication techniques
In Process: Official certificate of validation not yet provided but validation likely achieved
Validated: Adheres to the guidelines at a stringent level
