“The threat of severe ransomware attacks pose a clear and present danger to your organization.”
Such an ominous warning could be straight from the script of a high-budget action movie. Unfortunately, this is a real-world advisory from The United States Department of Justice in June 2021. Just days earlier, Christopher Krebs, the former head of the Department of Homeland Security's Cybersecurity and Infrastructure Security Agency, testified before Congress, that "we are on the cusp of a global pandemic of a different variety, driven by greed, an avoidably vulnerable digital ecosystem, and an ever-widening criminal enterprise."
A thriving Ransomware Economy has emerged. Ransomware hackers are getting smarter and now going straight for your backup data, so backup data must be inherently secure so attackers can’t hold data hostage. And while legacy backup solutions are good at recovering from natural disasters and IT failures, ransomware recovery requires you to rethink your security strategy. If data is the target, then security defenses must begin at the point of data.
The Need for Zero Trust Data Security
Traditional IT security defenses are failing. The bad guys are breaching firewalls and bypassing endpoint protections. The breakdown of the perimeter is driving a Zero Trust approach to cybersecurity. A Zero Trust architecture assumes all users, devices and applications are untrustworthy and can be compromised. In other words, trust nothing, always verify. Only multi-factor authenticated users get access to data, permissions limited, and specifically their ability to maliciously impact data is removed.
So, what does a Zero Trust architecture for data management look like? Rubrik adheres to the model defined by the National Institute of Standards (NIST), which is defined by the NIST SP 800-207 Zero Trust Architecture Specification. As NIST puts it, Zero Trust comprises “an evolving set of cybersecurity paradigms that move defenses from static, network-based perimeters to focus on users, assets, and resources.”
What is Rubrik Zero Trust Data Security?
Rubrik Zero Trust Data Security™ is an architecture that is modeled after the Zero Trust Implementation Model from NIST. At the core of Rubrik Zero Trust is Rubrik DataGuardian™, which supports a purpose-built file system that never exposes backup data via open network protocols. This creates a logical airgap that blocks data from being discoverable or accessible over the network.
Once data is written to the Rubrik system, it cannot be modified, deleted or encrypted by an attack, ensuring that a clean copy of data is always available for recovery. Multiple expert-guided recovery options, including Live Mount, Mass Recovery and AppFlows orchestrated recovery, are built-in so IT teams can quickly recover the files and workloads impacted by an attack.
What Rubrik Zero Trust Data Security means for:
IT teams can now protect critical data from ransomware attacks, giving their organization the ability to recover data and applications quickly without paying a ransom
Security teams can now confidently leverage secured backup data to perform attack forensics, and initiate recovery operations directly from their security operations center
Application owners can now rest easy knowing that business data is protected, and that if a ransomware attack were to occur, applications can be restored quickly to maintain business continuity
CIOs and CFOs can now be assured that ransomware recovery plans are supported by a Zero Trust architecture that enables the organization to minimize cyber insurance costs and prevent reputational damage resulting from ransomware attacks
Rubrik Zero Trust Data Security goes to the heart of data protection - keeping hackers out of your backup system, identifying ransomware activity, and making sure all data has a clean backup that can be recovered quickly. Read on for a deeper dive.
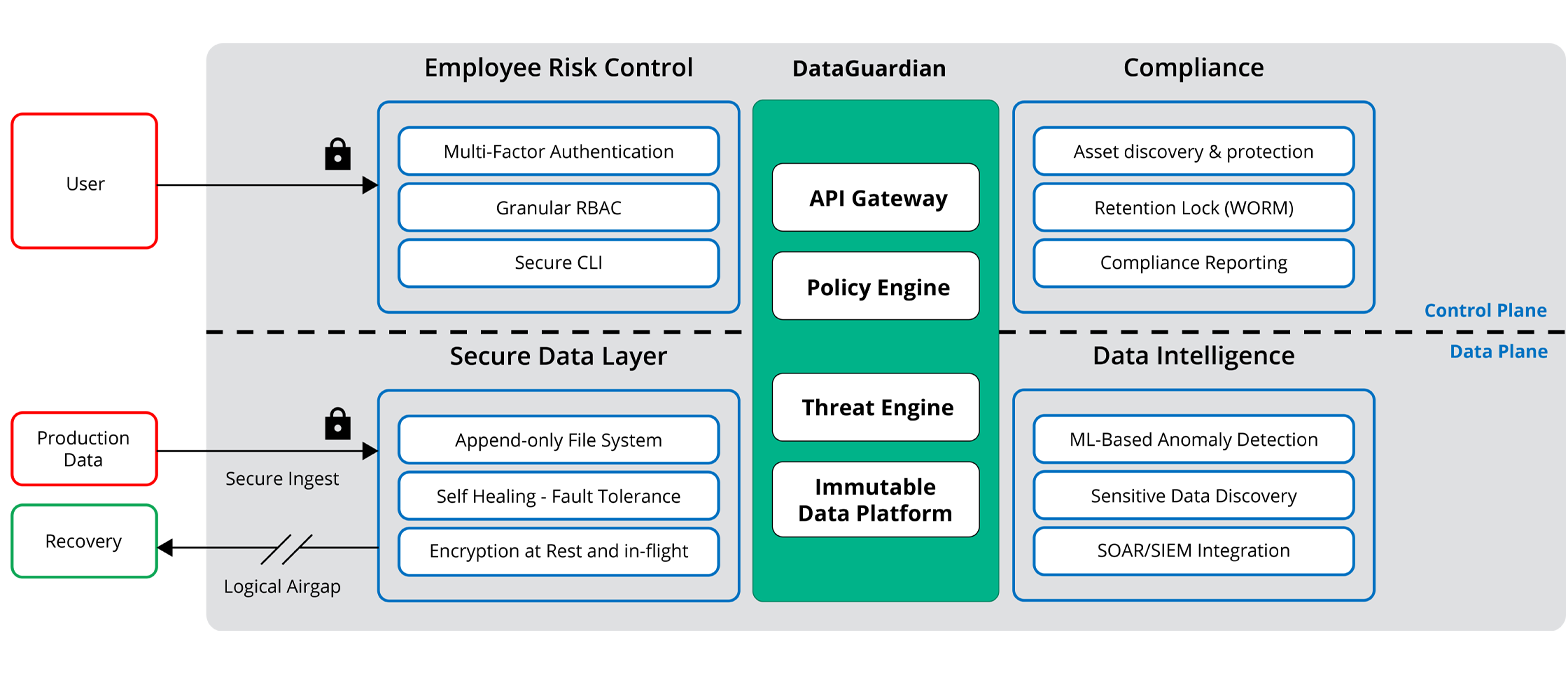
We start with some core pieces that are foundational to Rubrik Zero Trust Data Security.
Reduce the risk of intrusion – all system interfaces are secure, role-based, least privileged, and protected by 2FA - trust nobody and no system
Secure the data – data is always encrypted in-flight and at rest, and backup data is stored in a purpose-built append-only file system. Backed up data is always logically air-gapped so it’s offline and not accessible through standard network protocols
Detect and alert anomalous behavior – detect an attack, alert the Sec Ops team, and pinpoint a clean recovery point
Enforce compliance – automatically protect new workloads, lock retention, and find certain exposed sensitive data that may have been exfiltrated
Underlying the Rubrik Zero Trust Architecture is DataGuardian™, a core set of technologies that set Rubrik apart from legacy backup solutions.
Immutable data platform – Once ingested, no external or internal operation can modify the data. Data managed by Rubrik is never available in a Read/Write state to the client. This is true even during a restore or Live Mount operation. Since data cannot be overwritten, even infected data later ingested by Rubrik cannot infect other existing files or folders.
Declarative policy engine – Rubrik allows administrators to abstract away much of the low-end fuss required to build and maintain data protection, so they can focus on adding value at a more strategic level across the organization. The Rubrik policy engine is elegantly simple because all of the imperative details are abstracted away and handled by an incredibly smart, scale-out system. The resulting input fields are reduced to RPO objective, retention period, archive target, and replication target.
Threat engine – As each backup snapshot’s metadata is collected by Rubrik, we leverage machine learning to build out a full perspective of what is going on with the workload. The network is trained to identify trends that exist across all samples and classify new data by their similarities without requiring human input. The result is that Rubrik detects anomalies, analyzes the threat, and helps accelerate recovery with a few clicks.
Secure API-first architecture – Having an API-Driven Architecture means that every action in the Rubrik UI has a corresponding API that is documented and available for use. Or in other words, if you can do it through the Rubrik UI, you can programmatically do the same through the API that’s secured by role-based access and API tokens.
The message from the highest levels of government and security experts is clear: The bad guys are getting through traditional security defenses – and they are targeting your backup data as a growth strategy. It is time to rethink your data protection strategy, to set up new backup and recovery requirements based on Zero Trust principles, and to make IT investments that secure your data to help ensure your organization never has to pay a ransom.
