We are firmly in the AI era and the upcoming release of Anthropic's Claude Mythos marks a paradigm shift in AI security. The illusion that human speed prevention and detection can protect the modern AI enterprise has been shattered overnight. As Anthropic demonstrated, Mythos recently solved a corporate network attack simulation estimated to take a human expert 10 hours. This ability to outperform a human analyst is a feat not previously demonstrated by AI.
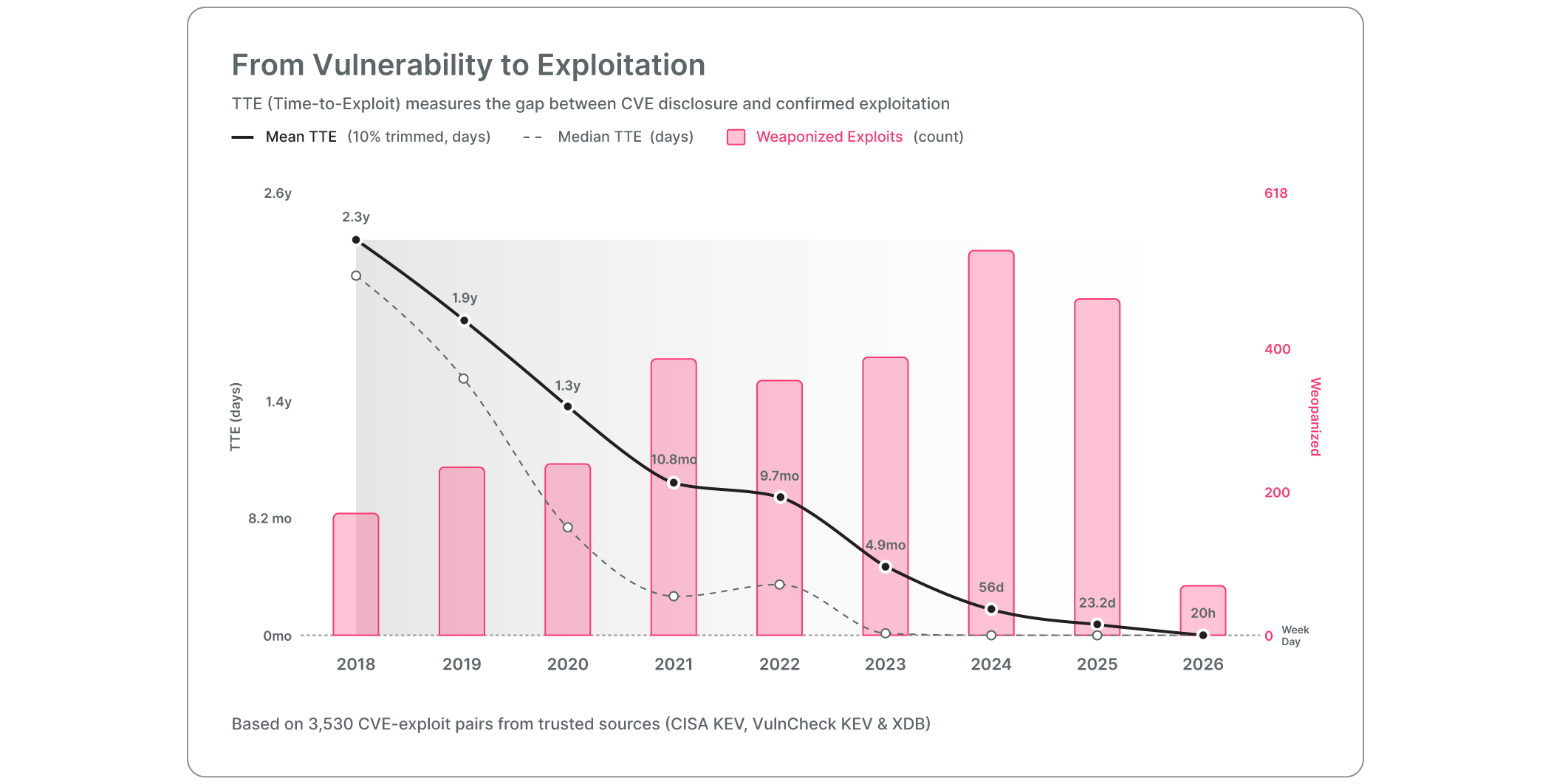
Time-to-exploit is decreasing rapidly in the agentic era. Source: www.zerodayclock.com
This accomplishment tracks with the overall trend in AI-powered cyber threats. In 2026, the median time-to-exploit collapsed from 1.6 days to 20 hours. AI is now capable of autonomously finding thousands of zero day security holes and generating exploits without any human intervention.
But the real threat isn't just that adversaries have faster tools. The real threat is the unmanaged, vulnerable AI agents already operating inside your network.
Unmanaged AI Agents are the New Attack Vector
According to the recent AI Vulnerability Storm briefing led by the Cloud Security Alliance (CSA), the most severe vulnerability facing enterprises today is the Unmanaged AI Agent Attack Surface—classified as a AAA Critical Risk. If an attacker wants your database today, they don't need to breach your firewall. They simply need to hijack your highly privileged, unmonitored AI agent and ask it to do the work for them.
This reflects an evolution in AI security. For the last couple of years, the industry has been focused on model safety, ensuring that our chatbots don’t hallucinate or say something inappropriate. But a safe foundation model means nothing if the deployment architecture is compromised.
As the CSA briefing warns, AI agents are "privileged, insecure by default, and not covered by existing security controls." The true danger lies in what your agent does; specifically the prompts, tool calls, retrieval pipelines, and resulting changes agents make to underlying data assets. This is where the most damaging security threats lie.
To defend against machine speed threats, human speed audits are no longer adequate. While the CSA explicitly recommends using LLM-based vulnerability discovery, runtime protection demands we go further.
You need AI to control AI.
Legacy security relies on static rules and pattern matching, which fail against AI agents operating in an unbounded action space. Agents are creative in how they chain APIs and construct prompts. A rigid regex filter cannot possibly anticipate a generative attack.
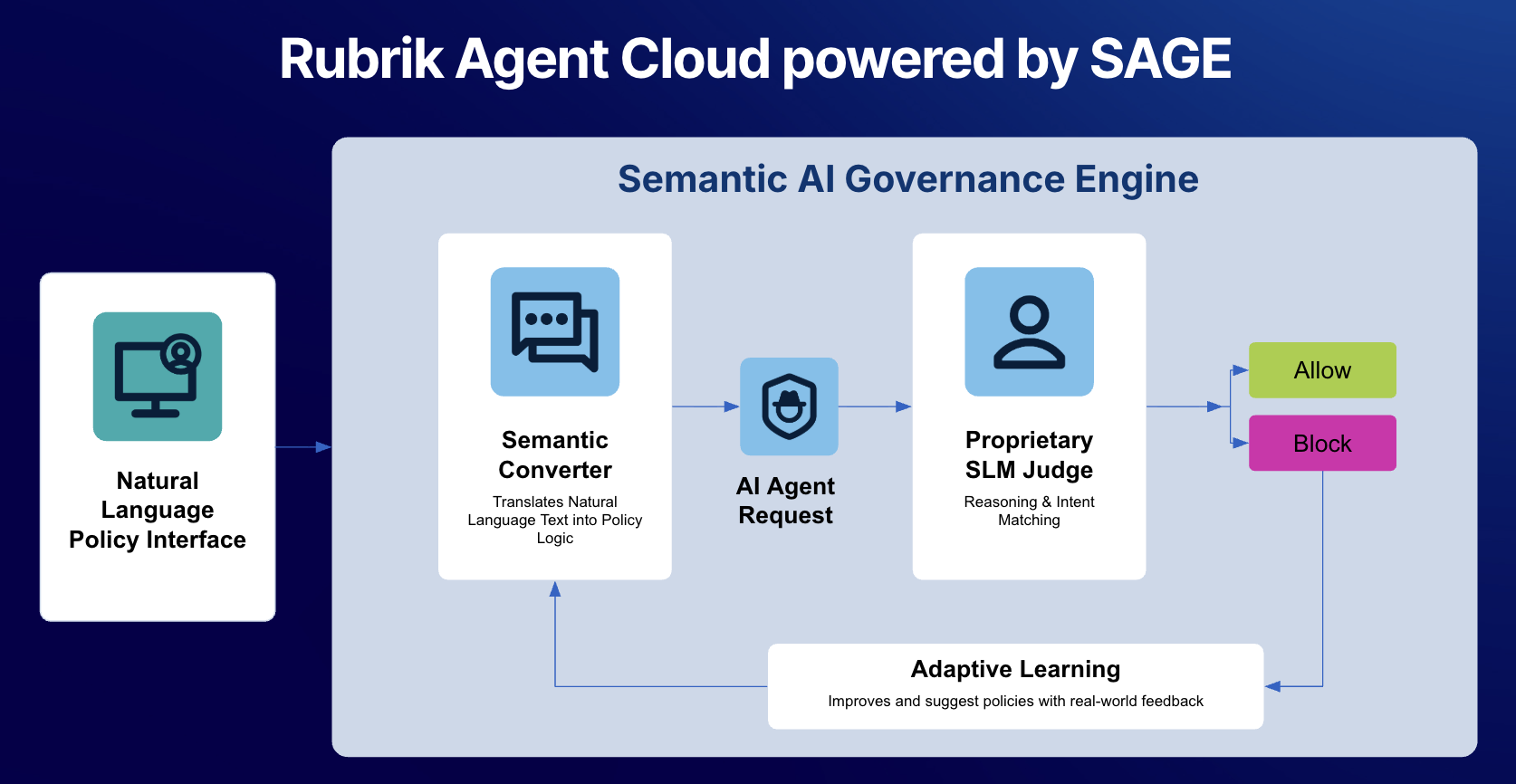
To secure this new attack surface, your control layer needs deep semantic understanding. This means moving beyond looking for known bad signatures or simple keywords and instead evaluating the true context and intent behind a prompt or sequence of actions. It requires a system that comprehends why an agent is making a specific API call, not just what the call is. By deploying a specialized LLM built specifically for governance, organizations can ensure that if a hijacked agent creatively attempts to exfiltrate data using a never-before-seen toolchain, the policy engine recognizes the underlying malicious intent and severs the execution.
Bonus Threat: AI Agent Sprawl
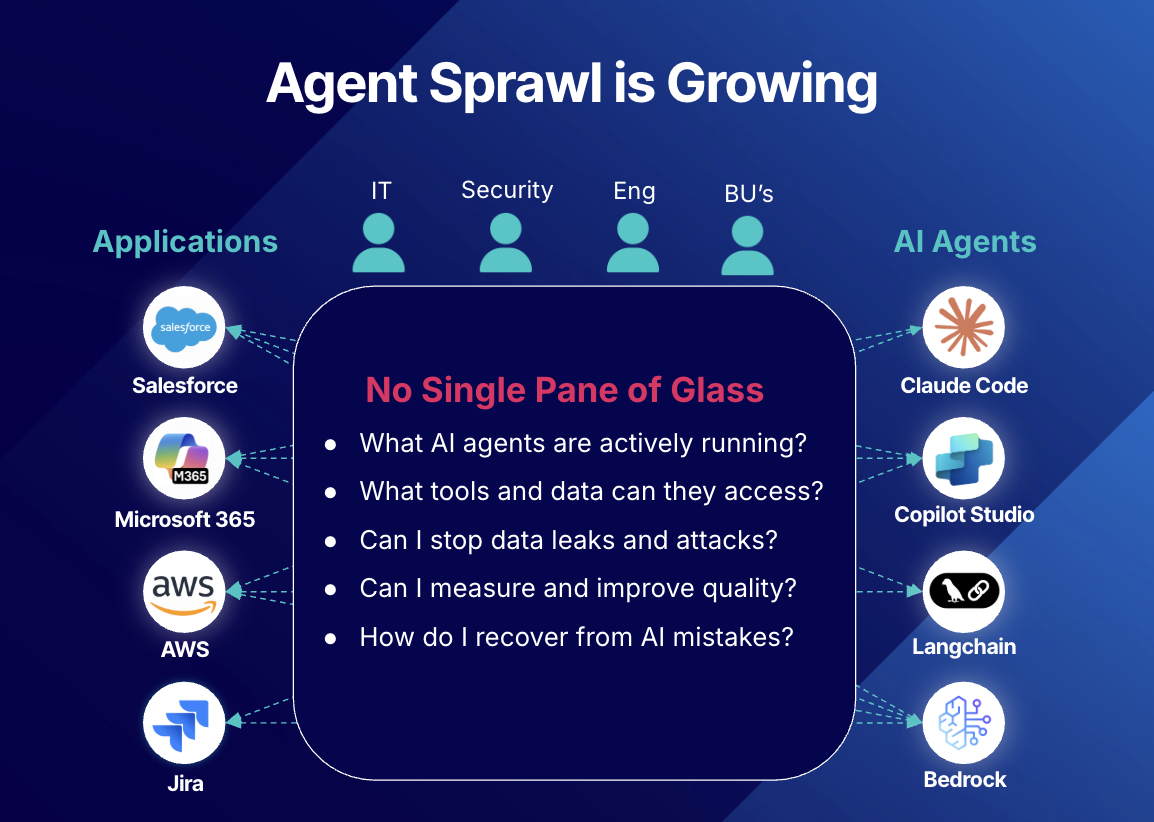
Adding to the risk factor is the proliferation of AI agents. Organizations don't use just one tool to build agents. Marketing teams are spinning up Microsoft Copilot Studio bots. ML engineers are stringing together workflows in LangChain. Developers are deploying custom Claude Code agents.
New agents with read/write access to your most sensitive data are being built every day, and security teams have zero visibility into their configurations, their actions, or their vulnerabilities. Without a single pane of glass, organizations are left with a fragmented, unmanaged attack surface.
Rubrik Agent Cloud: The Control Layer for Secure Enterprise AI
Rubrik Agent Cloud (RAC) was built for this exact inflection point. We don't believe in slowing down AI adoption. On the contrary, we believe robust security and governance unlocks 10x AI innovation. RAC transforms the fragmented, unmanaged AI agent landscape into a unified, governed workflow by addressing the three core pillars of secure agent operations:
- Holistic Posture Management: RAC helps eliminate the blind spots caused by multiplatform agent sprawl. By connecting directly to your existing agent building platforms (Copilot, n8n, Claude, Bedrock), RAC provides a single, unified management hub. We can instantly discover every new agent built, map its capabilities, and capture configurations and actions in real-time. You finally have a definitive, continuously updated security posture of your autonomous workforce.
- Intelligent Runtime Protection: As mentioned before, simple, static rules-based systems and regex filters cannot comprehend the nuances of adversarial prompts generated by agents. As CSA mentioned: you need an LLM to govern an LLM. RAC’s Semantic AI Governance Engine (SAGE) employs a purpose-built model that understands the semantic intent behind an agent’s action. If an attacker steals an employee's credentials and instructs their highly privileged Copilot agent to mass download and summarize restricted source code, standard identity systems see a valid login. RAC, however, recognizes the anomalous intent of the sequence—lateral movement and data exfiltration—and blocks the agent’s actions in real-time.
- Real-time Recovery and Resilience: When operating against AI-speed adversaries, prevention will eventually fail. A true resilience strategy requires a failsafe. If an agent is tricked into manipulating sensitive files or taking down a production database, RAC's industry first rewind capability allows you to surgically roll back the system state to the exact moment your data assets were compromised. You don't just stop the bleeding, you instantly repair the destructive action.
Securely Ride the AI Tailwind
Cybersecurity as we know it is dead. The advent of models like Mythos has permanently shifted the landscape, demanding that governance and resilience operate at machine speed. This isn't a reason to halt your AI initiatives. It's your opportunity to outpace the adversary.
With Rubrik Agent Cloud, you are architecting an intelligent security and control layer that empowers your business to harness the full potential of autonomous agents without the risk. The AI tailwinds are in our sails and the most important work is still ahead.
Don't wait for a compromised agent to dictate your security strategy. Schedule a custom demo of Rubrik Agent Cloud or take a self-guided product tour.
SAFE HARBOR STATEMENT
Any unreleased services or features referenced in this document are not currently available and may not be made generally available on time or at all, as may be determined in our sole discretion. Any such referenced services or features do not represent promises to deliver, commitments, or obligations of Rubrik, Inc. and may not be incorporated into any contract. Customers should make their purchase decisions based upon services and features that are currently generally available.
