Let’s say an unknown ransomware strain encrypts files across your environment. Or a mass deletion wipes out critical data. Or an automation agent silently overwrites files it shouldn't. When things like this happen in your enterprise, every team asks the same question:
“What actually happened to our data?”
Security tools help you identify compromised machines and track detection events. But during a destructive event, organizations need a complete picture of how data changed over time across all protected systems—data center, cloud, and SaaS. They need to know whether impacted files contained sensitive data, and they need a direct path from investigation to recovery.
This adds to the investigation delay, the biggest trap in the Mean Time to Recovery equation.
If you cannot see exactly what changed inside your data across snapshots, recovery will be a gamble. If you guess wrong, you risk overwriting healthy data—or reinstalling the ransomware and starting the nightmare all over again.
Rubrik Data Impact Investigation changes that. This new capability in Rubrik Security Cloud gives IT and security teams a single pane of glass to visualize, analyze, and recover from file-level changes, regardless of whether a security alert triggered the investigation.
Data Impact Investigation In Action
Let's walk through how this works in a cyber incident scenario.
Imagine that your SOC team has flagged 15 compromised machines. The endpoint detection tool caught the ransomware attack. Threat contained! Now you need to find out what happened to your data.
Here’s how that’s done:
Scope the Impact: The investigation dashboard provides a summary of all your protected objects (across data center, cloud, and SaaS workloads) with change metrics showing added, modified, and deleted files for each. You can filter by platform, search for the flagged objects, and sort by deleted files to surface the most impacted systems immediately.
Spot the Pattern: The snapshot activity view reveals a dramatic spike in deleted files paired with a corresponding spike in added files. The Trending File Extensions graph reveals an unknown ransomware extension appearing for the first time on that same date.

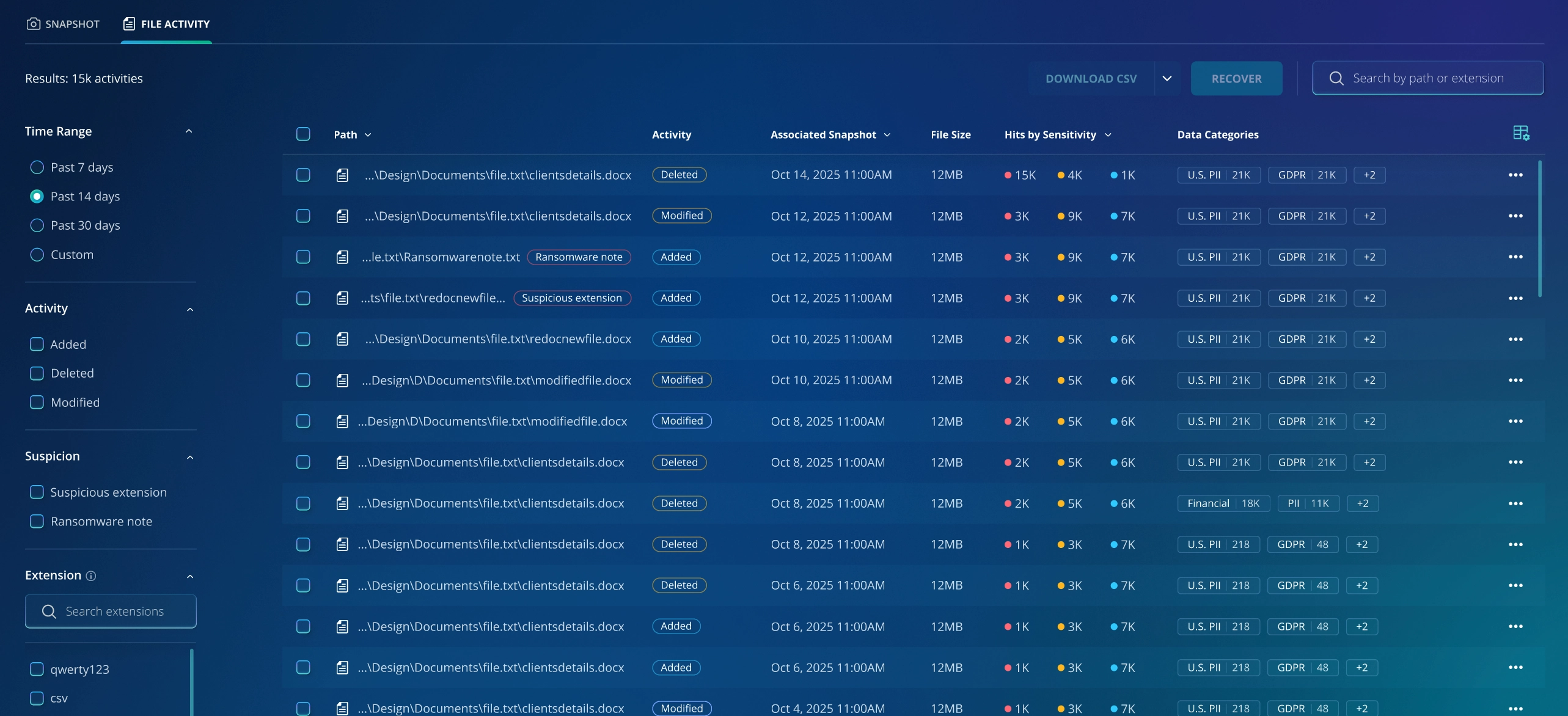
Pinpoint Data Exposure: The file activity view shows individual file change events across the selected time range. You can see file paths, activity types (added, deleted, modified), file size, and (critically) sensitivity classification. You can see if files with US PII and GDPR-regulated data were affected and instantly export the results as a CSV for compliance reporting.
Execute a Precision Recovery: The platform automatically recommends the snapshot immediately before the attack began—a clean recovery point confirmed by data, not guesswork. You select it and initiate a full object recovery or a granular file-level recovery, restoring only the impacted data without overwriting good files.
What could take days of manual guesswork now takes minutes of evidence-based investigation.
How it works alongside Anomaly Detection and Threat Hunting
When Anomaly Detection or Threat Hunting has findings, those insights are enriched directly into the Investigation views—flagged snapshots, suspicious files, and threat indicators appear in context alongside the file-level change data.
Here’s how these functions can work together:
Anomaly Detection: Think of Anomaly Detection as the smoke alarm; it identifies anomalous activity and raises an alert. Impact Investigation is the scene assessment. It lets you analyze file-level change activity across a broader time range to understand whether the damage started earlier or affected data beyond what the alert captured.
Threat Hunting: Threat Hunting answers a targeted question: is this specific known indicator of compromise (IOC) present in my backups? Investigation answers a broader question: what changed across my data during this time window? In a zero-day scenario where you don't yet have a known indicator to hunt for, Investigation gives you the panoramic view of change activity to identify the attack pattern.
Benefits Beyond Cyber Attacks
Data Impact Investigation isn't only for security incidents. It analyzes file-level changes across snapshots independent of any security alert, so it is equally powerful when no alarm ever fires.
Data Impact Investigation can help in the following scenarios:
Accidental Deletion: Imagine that a misconfigured script purges 50,000 files from a shared drive overnight. There's no attack, so no security alert fires. Impact Investigation surfaces the deletion spike, showing you exactly what was lost, when, and how to surgically recover it.
Unauthorized Changes by AI Agents: As organizations increasingly deploy AI and automation agents—coding assistants or cleanup bots, for example—the risk of unintended data loss grows. An agent with overly-broad permissions or a faulty instruction can delete or overwrite files at scale, silently and without triggering any security alert. Investigation gives teams a way to see exactly what an agent changed, when, and across which systems—turning an invisible problem into an actionable one.
What’s Next?
Data Impact Investigation is coming soon to Rubrik Security Cloud. Customers should make their purchase decisions based upon services and features that are currently generally available.
To learn more or see it in action, contact your Rubrik account team or visit rubrik.com.
